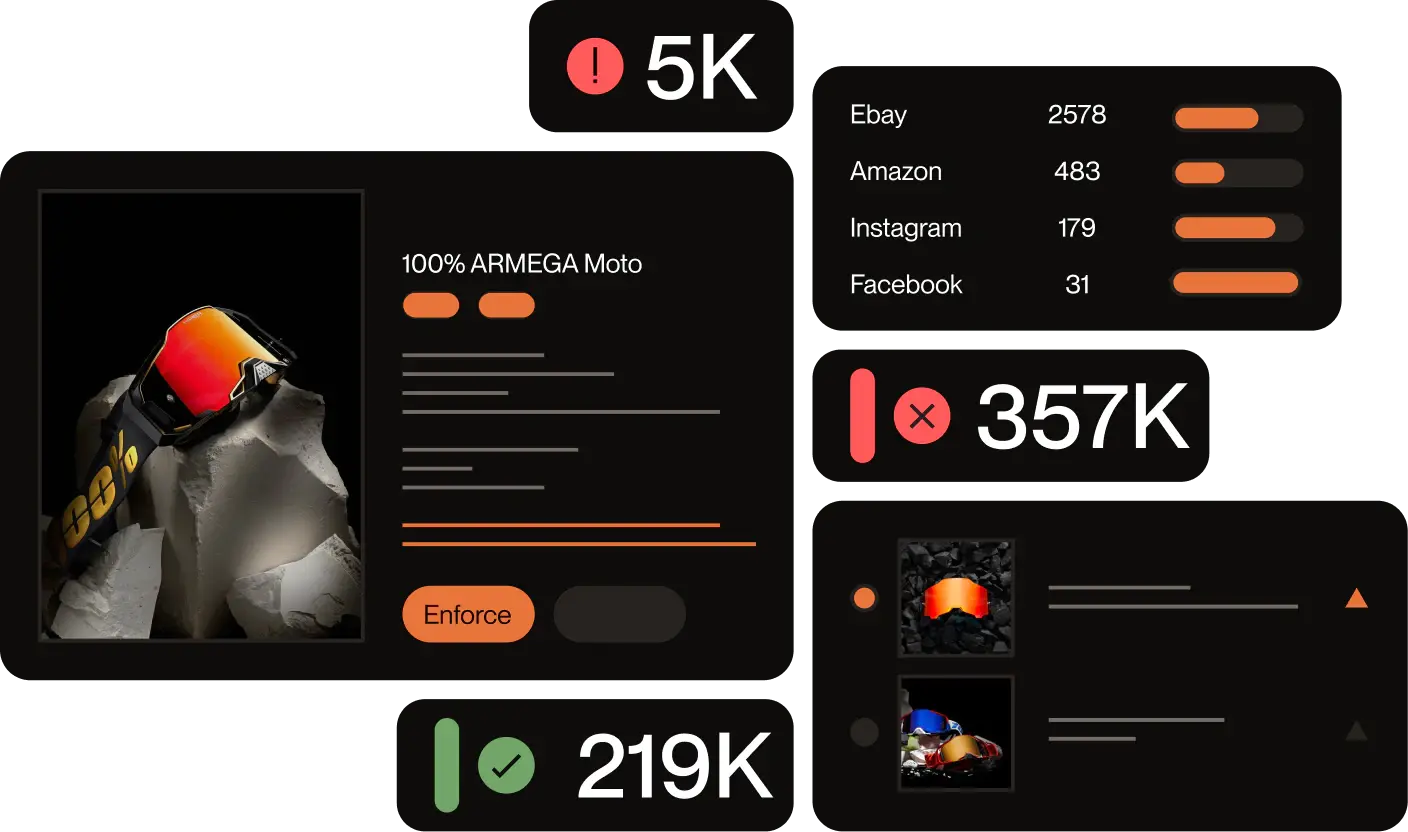
Key Outcomes
- 36,000+ Links Removed incl. 30k fake social profiles
- 92% Impersonation Reduction sustained over 18 months
- 99.6% Enforcement Success on social media
- 1 day Median Removal Time from detection to takedown
What This Case Study Covers
This case study explains how one of the world’s largest fashion groups, managing a complex multi-brand portfolio of apparel and homeware labels, eliminated 92% of ongoing brand impersonation across social media and the open web. The solution: a structured Managed Services approach powered by Red Points, combining daily specialist review, adaptive keyword tracking, and automated enforcement.
If you are evaluating brand protection companies, anti-counterfeiting solutions, or trademark management platforms for a multi-brand or enterprise portfolio, this case study details the exact tactics, results, and timeline that drove an 18-month sustained decline.
The Problem: Brand Impersonation at Scale Across a Multi-Brand Portfolio
The fashion group’s customers were being defrauded. Scammers built convincing replica websites that mirrored official brand stores down to login screens, capturing credentials, personal data, and payment details. Simultaneously, fake social media profiles surged: accounts posing as customer care teams, promoting fraudulent job offers, and running fake giveaways, mystery boxes, and discount scams.
Some bad actors embedded fake verification checkmarks directly into their account names. Others slid into the direct messages of users who complained on official channels, intercepting complaints before the real support team could respond. Fraudulent ads redirected shoppers to hidden fake sites.
The brand initially handled enforcement in-house, relying on its legal team to identify and report violations. But the volume and variety of tactics quickly made internal tracking unsustainable. Customer complaints kept arriving: orders that never came, credit cards compromised after purchases, and the in-house approach had no path to scale.
The Solution: Structured Managed Services for Multi-Brand Trademark Protection
Daily Manual Review by a Dedicated Brand Protection Specialist
Red Points assigned a dedicated Managed Services specialist who reviewed detected profiles and domains every day. The review process checks what an account is selling, when it was created, and what its apparent intent is. The specialist applies a consistent set of fake indicators to distinguish genuine fan pages from bad actors:
- Accounts with zero or very few followers
- Profiles using the official brand logo as their profile picture
- Handles embedding a country name alongside the brand name
Once a violation is confirmed, enforcement runs automatically, freeing the legal team entirely from day-to-day operational monitoring.
Weekly Keyword Refinement Across 7 Threat Categories
Because scammers rotate tactics constantly, shifting from giveaway fraud one week to fake job offers the next, detection cannot rely on a fixed keyword list. The specialist updates tracking terms weekly across several distinct threat categories:
- Fraud & Engagement Bait: Fraud and engagement bait like Brand name + “gift card,” “giveaway,” “mystery box,” “sales,” percentage signs
- Job & Recruitment Fraud: Combinations with “job,” “recruitment,” “model” — flagging fake hiring accounts used to harvest personal data
- Customer Care Impersonation: “Customer care,” “support,” “helpdesk,” “claim,” “service” — surfacing fake support accounts that intercept real complaints
- Authenticity-Bait: “Genuine,” “authentic,” “original,” “outlet” — keywords scammers use to signal legitimacy to buyers seeking verified products
- Seasonal Campaigns: “Black Friday,” “Cyber Monday” — added ahead of peak sale periods when fraudulent activity spikes
- Geographic Targeting: Brand name + 40+ country names (France, Germany, Nigeria, Indonesia, Saudi Arabia, and others) — catching locally targeted scams that global monitoring alone misses
- Typosquatting & Misspellings: Truncated and phonetically altered brand name variations that evade standard keyword filters
Expanding Protection to Ads and Emerging Viral Formats
Enforcement extended beyond profiles to fraudulent social media ads designed to redirect users to hidden fake sites. The specialist team also monitored emerging viral formats. For instance, a trend where videos encouraged users to “run to the store” for products the brand did not actually sell. Once the pattern was identified, detection was extended using hashtag and keyword combinations tied to that specific format.
The Results: 92% Sustained Reduction in Brand Impersonation
Eighteen months into the program, monthly infringements had dropped from roughly 4,000 to around 200 and stayed there. That 92% sustained reduction was the clearest signal that the approach was not just delivering short-term wins; it was changing scammer behavior. When violations are closed faster than bad actors can regroup, enforcement itself becomes a deterrent.
| Channel | Links Removed | Success Rate | Median Removal |
| Social Media (all) | ~30,000 profiles | 99.6% | 1 day |
| Fraudulent Websites | Included in 36,000+ | 96.4% | < 3 hrs (detection to validation) |
| Overall (all channels) | 36,000+ links | 94.6% (first attempt) | 1 day |
Beyond the numbers, the legal team, once stretched across daily monitoring tasks, now focuses exclusively on higher-level work. And the drop in infringing activity has held steady rather than spiking back, which suggests that the speed and volume of enforcement has itself become a deterrent to new bad actors entering the space.
Frequently Asked Questions (FAQs)
A dedicated specialist handles the day-to-day monitoring and enforcement on your behalf. They review detected threats, confirm violations before any action is taken, and continuously refine detection rules to keep up with how scammers evolve. Your internal team sets the direction; the specialist handles the operational work.
What types of brand impersonation can brand protection software detect?
Most platforms cover fake social media profiles, fraudulent websites, impersonation ads, and typosquatted domains. More advanced solutions also detect customer care impersonation accounts, fake recruitment pages, and visual violations like unauthorized logo use in images — without relying solely on text-based keywords.
It can, but coverage depends on how detection is set up. Effective global monitoring accounts for local language variations, region-specific scam tactics, and the fact that bad actors often target markets where enforcement pressure is lower. A one-size-fits-all keyword list will miss a significant share of locally targeted fraud.
Scammers adapt quickly, so detection has to be treated as an ongoing process rather than a one-time setup. Regular refinement — updating keywords, identifying new patterns, and running proactive searches — is what separates a system that stays effective from one that only catches yesterday’s threats.
Internal teams can handle enforcement up to a point, but as threat volume grows across platforms and markets, the monitoring workload becomes difficult to sustain alongside other priorities. Outsourcing makes sense when in-house tracking is reactive, when complaints are coming in faster than violations are being removed, or when the team responsible has higher-value work that brand monitoring is pulling them away from.