TL;DR
- Counterfeit and pirated goods cost the global economy over $467 billion annually and represent roughly 2.3% of global trade
- Bad actors now use generative AI to produce fake storefronts, synthetic product images, and recolored logos in minutes, which means static, rules-based detection no longer works
- Effective enforcement in 2026 requires always-on automation, visual AI detection, and API-based takedowns, not manual workflows capped by analyst hours
- The 12 strategies below cover every major attack surface: marketplaces, domains, social commerce, paid ads, influencer abuse, and gray market channels
The 12 strategies
1. Secure a global IP foundation
Registering trademarks and copyrights in your home country alone is not sufficient. Without registered rights in the specific territory where an infringement occurs, platforms can delay takedown requests, and courts will not hear infringement claims.
This means registering IP across every manufacturing hub and destination market. China deserves specific attention: over 70% of physical counterfeits originate there, and brands that have not registered in China cannot pursue removal through Chinese courts or customs channels even if the product was never intended for the Chinese market. Counterfeiters copy designs from product photos alone, with no need to see the physical item.
Red Points’ Premium Domestic China Protection addresses this directly, combining local expertise and compliant enforcement processes to detect and act on infringements within mainland-only platforms that are otherwise inaccessible to international teams.
Centralizing your IP portfolio in a system connected to enforcement workflows removes the most common friction point in day-to-day enforcement: automatic verification that you hold the right registration in the territory where an infringement was detected, before a takedown request is submitted.
Red Points’ Document Management capability does this by consolidating IP rights, trademarks, patents, and copyrights into a single operational hub linked directly to enforcement activity, so teams can act without delays caused by missing or outdated documentation.
2. Implement preemptive domain management
The most dangerous counterfeit sites are deliberately non-indexed and receive traffic exclusively through paid ads, QR codes, and direct messages, which means any monitoring approach that relies on search visibility will never find them.
Comprehensive domain management requires two programs running in parallel. The proactive side involves registering domain variants before counterfeiters can buy them: common misspellings, abbreviations, TLD variations (.net, .org, .co, country-specific TLDs in key markets), and your brand name combined with words like “shop,” “official,” or “sale.” Registering these costs far less than disputing them later through UDRP proceedings. The reactive side involves continuous scanning across all registered domains, not just search engine results, to detect typosquatting and lookalike sites as soon as they appear. Red Points scans over 1.4 billion domains with 99.5% ccTLD coverage for exactly this reason.
Real-world impact: Cotopaxi used automated domain detection to group scam domains by template pattern, recovering over 130 hours of manual work in a single quarter and preventing $13.5 million in potential fraudulent transactions.
3. Monitor social commerce and infiltrate counterfeit networks
Branded keyword-based monitoring sometimes misses the most active counterfeit sellers on social media, because counterfeiters on these platforms do not need to use your brand name. They use video and images to sell, which only image-based detection can catch.
Social commerce brand protection requires continuous detection across all channels using image fingerprinting, logo detection, and OCR applied across posts, reels, and stories. These tools catch your visual assets even when the brand name has been deliberately removed from all text. Four specific threats that basic monitoring misses deserve their own coverage:
- Closed counterfeit networks: Bad actors organize selling operations in private social media groups and messaging app communities that are invisible to public monitoring. Creating undercover accounts to access these groups exposes the full scale of a coordinated operation, often hundreds of connected sellers, before enforcement begins.
- Verified accounts: Securing verified account status on all major platforms also matters. The blue checkmark is the fastest signal to a potential buyer that your page is the official brand, not one of the impersonator accounts counterfeiters create using your logo and images.
- Executive impersonation: Social impersonation extends beyond brand accounts. Bad actors increasingly create fake executive profiles on LinkedIn and X, posing as CEOs, CFOs, and other senior leaders, to issue false instructions, request sensitive information, or initiate fraudulent payments. Because these profiles closely mimic real identities, they are difficult for employees to detect and can cause financial damage before anyone realizes the profile is fake. Red Points’ Executive Impersonation Protection monitors for leadership identity abuse across social platforms, extending protection to the people behind the brand as well as the brand itself.
4. Automate marketplace takedowns via direct API integrations
Manual submission through platform reporting forms consistently creates backlogs during surge periods, and when a counterfeiter can relist within hours of a takedown, enforcement speed matters more than the volume of requests filed.
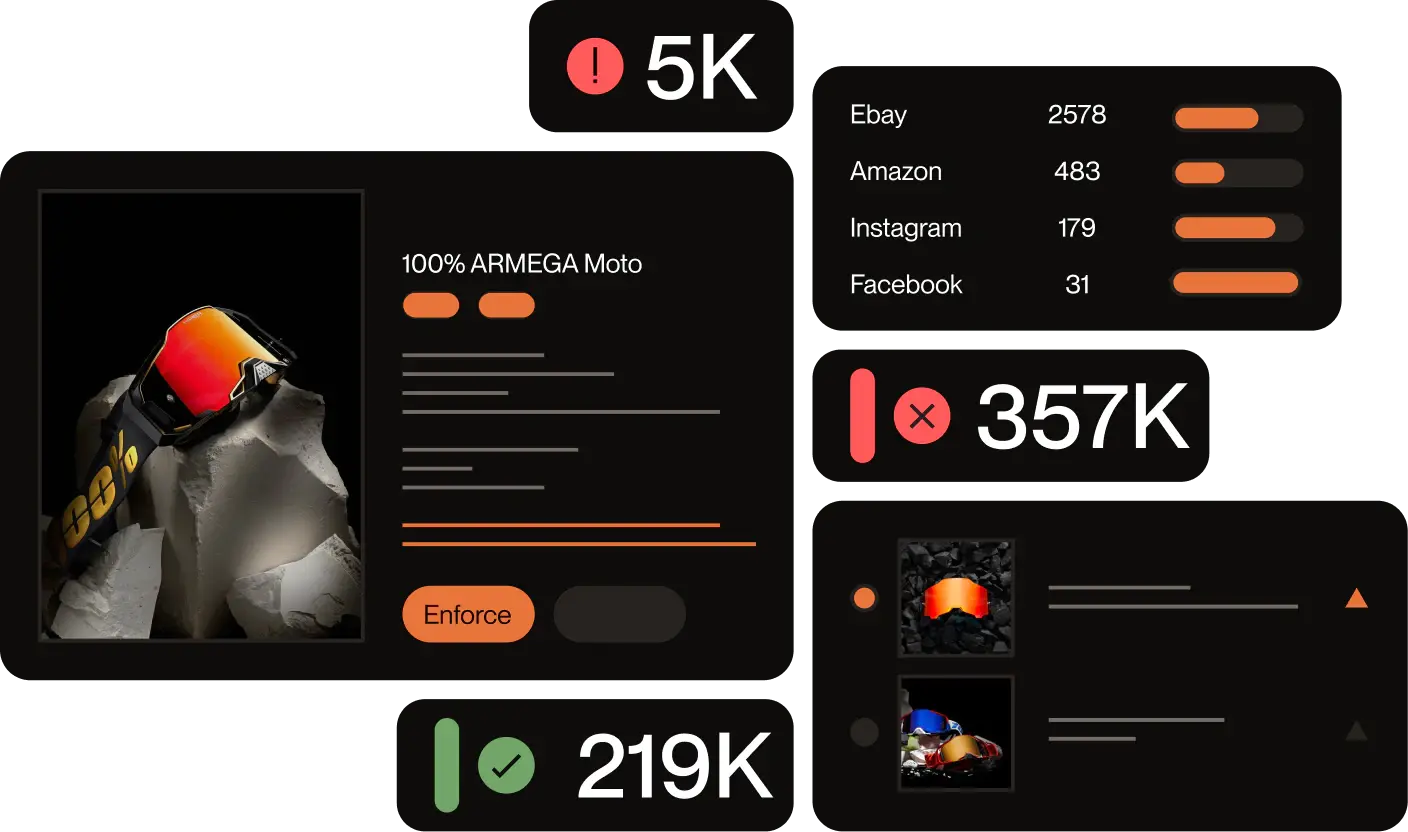
Direct API integrations with platforms, combined with priority program participation such as Amazon Project Zero, Amazon Brand Registry, and eBay VeRO, compress removal timelines from days to hours for the highest-confidence cases. Red Points processes over 100 million listings per day and enforces 8.1 million incidents per year, with an average takedown time of 1.5 days, which is only achievable through automation, not analyst hours. The enforcement model matters as much as the technology: per-takedown pricing or analyst-hour caps create escalating costs during surge attacks, exactly when brands need the most capacity. A flat-fee unlimited model absorbs those spikes without the cost scaling proportionally.
Real-world impact: Burton used Red Points’ direct API connections and platform priority programs to remove over 4,600 fraudulent websites and prevent more than 5,000 fraudulent transactions before customers were harmed.
5. Dismantle seller networks and recover revenue from repeat offenders
Seller network analysis identifies the shared infrastructure, payment accounts, IP addresses, product images, and phone numbers that connect seemingly independent counterfeit accounts into coordinated operations. Red Points’ Actor Networks capability connects these dots across marketplaces, social platforms, video sites, and messaging apps, giving brands a consolidated view of how sellers relate to one another so enforcement can target the distribution network, not just the visible listing. By analyzing over 2.7 billion data points monthly, Red Points clusters seller identities and exposes shared nodes.
For the highest-volume repeat offenders, those who survive multiple takedown cycles, revenue recovery programs, such as Red Points’, escalate beyond listing removals to freeze infringer assets and pursue legal settlements. Recovered funds offset the cost of enforcement, making the program self-financing for brands with sufficient infringing volume. The outcome is permanently closed seller accounts rather than recurring removal of the same actors.
6. Score sellers by risk to prioritize enforcement
Predictive seller risk scoring ensures enforcement resources concentrate on the actors causing the most financial damage, not spread equally across all violations, most of which are low-volume and low-recurrence.
Not every infringement warrants the same response. A one-time listing from a new account differs entirely from a seller with 500 listings across six platforms who has relisted four times after previous takedowns. Red Points’ Seller Risk Score consolidates behavioral signals, recidivism rate, listing volume, cross-platform activity, pricing patterns, and account age into a single percentile-based assessment that makes it straightforward to identify which sellers pose the highest risk and act before issues escalate. Sellers with high recidivism and large listing volumes are escalated to the network analysis and revenue recovery program in Strategy 5. Low-risk, one-off sellers receive standard automated takedowns.
Red Points’ AI Incident Prediction works alongside Seller Risk Score to prioritize at the incident level rather than just the seller level. It assigns a predictive risk level to each incoming incident based on the brand’s unique threat patterns, product catalog, and historical validation trends so teams can focus on cases most likely to affect revenue or consumer trust without reviewing thousands of incidents sequentially. Both models improve continuously as enforcement outcomes feed back into the scoring algorithms.
7. Deploy Visual AI and OCR to catch design-copy listings
Visual AI is the only detection method that works when counterfeiters deliberately remove all brand names and trademarks from a listing. It identifies infringements based on what the product looks like, not what the text says.
Computer vision models trained on a brand’s specific visual assets, like logo variants, product shapes, packaging geometry, and color patterns, identify infringements even when the counterfeiter has modified the image to evade detection: recoloring a logo, adjusting font weight, changing background colors. These models analyze visual similarity against a spectrum rather than matching exact pixels, which means they continue working as bad actors iterate their evasion techniques. Red Points’ Vision AI goes a step further by showing teams the specific visual cues — logos, patterns, design elements, embedded text — that triggered a match, making image-based detection transparent and reducing the back-and-forth of manual case review.
OCR adds a second detection layer by reading text embedded in images (brand names visible in product photography, packaging text not included in the listing description, or trademarks that appear in lifestyle images) that standard text parsing misses entirely.
Real-world impact: Graff Diamonds used Visual AI to identify jewelry replicas that precisely copied their design geometry but omitted the Graff name from all listing text. The result: $6 million in counterfeit value removed and 3,500+ unauthorized sellers blocked.
8. Detect non-indexed sites and paid ad redirects
Fraudulent sites that never appear in search results get thousands of visitors through paid ads that display a legitimate-looking URL but redirect buyers to a counterfeit storefront, reporting the ad alone leaves the underlying site fully operational.
The attack pattern works like this: a counterfeiter purchases ads on Google, Facebook, or Instagram using your branded keywords. The display URL appears identical to your real domain; the actual destination URL is a fraudulent storefront. Automatic extraction of actual destination URLs from all ads using branded keywords — not display URLs — combined with linked incident creation for each confirmed fraudulent destination, enables enforcement against both the advertisement and the underlying site in a single workflow. This attack concentrates during high-traffic periods, product launches, Black Friday, seasonal sales, when counterfeiters increase paid ad spend, knowing buyer intent is highest.
9. Monitor the gray market and parallel imports
A gray market product is a genuine item sold through an unauthorized distribution channel, not a fake, and the damage it causes is different from counterfeiting: it erodes pricing integrity, violates distribution agreements, and undermines relationships with authorized retailers.
The business consequences are concrete. A distributor with exclusive regional rights will question the relationship when identical genuine products appear on the same marketplace at lower prices from an unknown source. A retailer that paid for exclusive regional distribution may stop placing orders if it believes the brand is competing against it through back channels. Monitoring pricing signals and distribution patterns across global marketplaces, flagging sellers who match known unauthorized sources or who show pricing anomalies consistent with parallel import activity, enables distribution agreement enforcement at a scale that manual monitoring cannot reach.
10. Detect and counter advanced evasion tactics
Counterfeiters use specific technical methods such as geoblocking, parked domains, and user-agent string manipulation that are designed to defeat standard monitoring and detection systems, not explicitly built to counter each one, will consistently miss an entire segment of infringing activity.
Each evasion tactic requires its own countermeasure:
- Geoblocking makes fraudulent sites invisible to requests from the brand’s home country. Defeating it requires crawling from multiple geographic IP locations.
- Parked domains appear inactive to a single-point-in-time crawl but activate under specific conditions or time windows. Defeating it requires monitoring domains across time, not just a snapshot.
- User-agent string manipulation creates mobile-only or app-only storefronts that desktop-based crawlers never see. Defeating it requires crawlers that simulate multiple devices and browser environments.
- AI-generated evasion adds a further layer: slightly different logo colors, modified font weights, and one-letter domain variations all defeat systems built around fixed similarity rules. Detection models need to analyze visual patterns against a spectrum of similarity, not match against a fixed template, to stay effective as bad actors iterate.
11. Build social proof and prevent review manipulation
Counterfeiters actively weaponize customer reviews, using fake positive reviews to boost their fraudulent listings and fake negative reviews to damage legitimate brand pages, because review ratings have a direct, measurable impact on purchase volume.
Research shows that a one-star increase in average rating correlates with a 26% boost in sales on Amazon. On Amazon’s combined listing system, a buyer can purchase from a fraudulent seller on the official product page, receive a counterfeit, and leave a negative review against the legitimate brand. Customer service then handles a complaint about a product that was never genuine. Monitoring for coordinated negative review spikes, multiple low-rated reviews in a short window, accounts with no purchase history, reviews describing quality issues inconsistent with the genuine product, allows brands to identify and report manipulation before it damages a listing’s overall rating. Providing customers with clear ways to verify authenticity, like dedicated verification pages, QR codes on packaging, and comparison guides, reduces the window of confusion counterfeiters rely on to convert buyers.
12. Measure enforcement ROI and secure stakeholder buy-in
Brand protection programs get deprioritized or cut not because they fail to produce results, but because they fail to translate those results into financial terms that leadership can evaluate against other budget priorities.
The metrics that resonate connect enforcement directly to business outcomes: enforcement success rate (Red Points achieves 95% on average across platforms, the success rate is highly variable, depending significantly on the channel type (e.g., rogue websites versus established e-commerce marketplaces) and factors specific to the domain, such as the hosting country and the platform’s policies.), time-to-removal by platform, estimated revenue at risk from confirmed infringing listings, and repeat infringer rate (the percentage of removed sellers who relist within 30 days).
Red Points’ Custom Tags give teams a practical way to structure this reporting by labeling and grouping incidents by urgency, product line, workflow stage, or escalation type so that trend analysis and stakeholder reports reflect the organization’s own priorities rather than generic platform categories. Presenting these alongside case studies where enforcement prevented measurable revenue loss, such as network dismantling before a peak sales period, site takedowns during a product launch, closes the loop between operational activity and financial impact.
Real-world impact: ASICS used structured enforcement reporting to demonstrate the removal of over $2.5 billion worth of counterfeit products, securing continued internal investment and organizational buy-in for their brand protection program.
Manual vs. Red Points’ AI-driven enforcement: the key differences
| Dimension | Manual enforcement | AI-driven enforcement (Red Points) |
| Detection coverage | Indexed platforms only; misses non-indexed sites, image-only listings, and closed social groups | Covers non-indexed domains, visual listings, social video content, and closed networks; Red Points scans 1.4B+ domains and processes 100M listings per day |
| Detection speed | Hours to days; dependent on analyst availability and shift coverage | Continuous 24/7 scanning; new infringements flagged in minutes |
| Logo and design detection | Cannot identify recolored, modified, or stylistically altered logos | Vision AI identifies logo variants and design-copy listings with no brand name present; shows visual cues behind each flagged incident |
| Seller network analysis | Impractical at scale; relies on manual cross-referencing of accounts | Actor Networks clusters seller identities across 2.7B+ data points per month; exposes coordinated operations, not just individual accounts |
| Takedown speed | Days to weeks via manual platform reporting forms | Average 1.5 days via direct API integrations and platform priority programs; 8.1M incidents enforced per year |
| Cost at scale | Scales linearly — more infringement volume requires more analyst hours | Flat-fee unlimited model; cost does not increase proportionally with attack volume |
| Evasion tactic detection | Misses geoblocking, user-agent manipulation, and parked domains | Multi-location, multi-device crawling explicitly designed to detect evasion |
| Enforcement consistency | Variable by analyst, region, and platform familiarity | 95% average enforcement success rate applied consistently across all platforms and regions |
Frequently asked questions (FAQs)
Brand protection is the continuous process of detecting, validating, and removing unauthorized use of a brand’s intellectual property, including counterfeits, impersonation, domain abuse, gray market sales, and ad-hijacking, to preserve revenue, customer trust, and brand equity.
The most effective approach combines automated AI detection with API-based enforcement. This allows brands to monitor millions of listings continuously and execute takedowns in hours, using computer vision and OCR to identify threats that keyword-based monitoring would miss entirely. No single strategy is sufficient on its own; the 12 strategies above address different attack surfaces that each require dedicated coverage.
Gray market goods are genuine products sold through unauthorized distribution channels at prices that undercut official distributors or violate territorial agreements. Unlike counterfeits, gray market goods are real, but their unauthorized sale undermines pricing integrity, damages authorized retailer relationships, and may violate distribution contracts.
Most traditional solutions fail due to three main root causes: limited detection comprehensiveness that leaves them blind to emerging threats, slow detection-to-takedown speeds caused by heavy manual effort, and inconsistent enforcement success due to weak platform integrations and a lack of expert follow-up.
Brandjacking is when someone hijacks or impersonates a brand’s identity online. Scammers create fake websites and social media profiles to mimic a legitimate business, often tricking customers into handing over personal information. Because a brand’s reputation is incredibly difficult to build but fast to lose, brandjacking causes severe financial and reputational damage before a company even realizes it is happening.
Consumers often buy fakes unintentionally; in fact, 46% of US shoppers surveyed bought fakes by accident. They are tricked by highly realistic listings, with 57% of shoppers trusting them because the product photos look like the official brand, and 47% being fooled by clear descriptions and official-looking branding. Shoppers are finding these deceptive listings everywhere, including social media (49%), search results (48%), and even AI recommendations (26%).