Someone has built a website that looks exactly like yours. They are using your logo, your product photos, and your brand name to deceive your customers into handing over their money or personal data. By the time you find out, the damage to your reputation and your customers’ trust is already done.
Brand impersonation is one of the fastest-growing forms of cybercrime, and it targets businesses of every size. AI is accelerating the problem: Red Points’ 2025 research found that 28% of counterfeit buyers used AI tools to assist in their search for fakes, while generative AI has made it faster and cheaper than ever for bad actors to build convincing fake websites, fake social media profiles, and fraudulent ads at scale. This guide explains what brand impersonation is, the different forms it takes, how to detect it early, and exactly what to do when you find it.
TL;DR
- Brand impersonation is when someone poses as your business online to deceive your customers or steal sensitive information
- It takes many forms: fake websites, social media accounts, mobile apps, phishing emails, fake ads, and domain spoofing
- Impersonation scams resulted in $2.95 billion in consumer losses in 2024, making them the most commonly reported fraud category in the US for the second consecutive year
- Nearly 1 in 3 shoppers stop buying from the original brand after a bad counterfeit experience, making reputational damage one of the highest long-term costs of impersonation
- Detection requires continuous monitoring across all digital channels, as manual checks miss the majority of violations
- Repeat impersonators typically relaunch under new domains or accounts within days of a takedown, which is why discovery and reporting need to run continuously, not reactively
What is brand impersonation?
Brand impersonation is a type of attack in which scammers pose as a legitimate business to deceive consumers or employees. The goal is typically to extract money, steal sensitive information, or damage the impersonated brand’s reputation. Impersonators exploit the trust that customers already have in a known brand, which makes their scams significantly more convincing than generic fraud attempts.
Brand impersonation is not a single tactic. It is an umbrella term covering fake websites, fraudulent social media profiles, counterfeit mobile apps, phishing emails, fake advertisements, and domain spoofing. What these methods share is that they all misuse a real brand’s identity without permission and at the brand’s expense.
The scale of the problem is substantial. According to the FTC’s 2024 Consumer Sentinel Network Data Book, imposter scams resulted in $2.95 billion in consumer losses in 2024, making them the most commonly reported fraud category that year for the second consecutive year.nd’s get automated software to monitor and takedown any offending profiles, websites, or apps.
What are the different types of brand impersonation?
Understanding which form of impersonation you are dealing with determines where and how you report it.
| Type | How it works | Where it appears |
|---|---|---|
| Fake websites | A copy of your site built to harvest credentials or sell counterfeits | Open web, search results, social media ads |
| Domain spoofing | A domain designed to look like yours (e.g. “brandname-store.com” or “brandnarne.com”) | Emails, URLs in ads |
| Social media impersonation | Fake accounts using your logo and name to message customers or run scams | Instagram, Facebook, X, LinkedIn, TikTok |
| Mobile app impersonation | A fraudulent app mimicking your legitimate app to steal login credentials or payments | Apple App Store, Google Play, third-party stores |
| Phishing emails | Emails sent from look-alike domains impersonating your brand to trick recipients | Email inboxes |
| Fake advertisements | Paid ads using your brand name or visuals to drive traffic to infringing sites | Google, Meta, TikTok Ads |
| Business email compromise | Emails impersonating your executives or suppliers to trick employees into transferring money | Internal email systems |
What are real-world examples of brand impersonation?
Brand impersonation happens across every industry and at every scale.
Fake online stores are one of the most common forms. Scammers build a convincing Shopify or standalone ecommerce store using your product images, branding, and pricing structure. Customers order products and either receive cheap counterfeits or nothing at all. The complaints often land on the real brand rather than the scammer.
Phishing emails impersonating financial institutions, software companies, and logistics providers are another frequent form. Scammers use templates that closely replicate legitimate brand emails to trick recipients into clicking malicious links or entering credentials on fake login pages.
CEO fraud is a well-documented escalation of brand impersonation targeting businesses from the inside. A scammer impersonating a company’s chief executive emails a finance employee requesting an urgent wire transfer. Even highly sophisticated organizations have been victims. In one widely reported case, a scammer impersonating a third-party vendor defrauded Google and Facebook of more than $100 million over several years before being caught.
Fake mobile apps are particularly common in fintech and banking. An app that closely mimics a legitimate banking or payments app is listed in app stores to harvest login credentials from users who believe they are downloading the real product.
What damage does brand impersonation cause to businesses?
The impact of brand impersonation extends well beyond the immediate financial losses suffered by victims.
Revenue loss: Customers who are deceived by impersonators may never know they bought from a fake. They simply do not reorder from the legitimate brand, attributing poor quality or non-delivery to the real company. According to Red Points’ 2025 Counterfeit Buyer Teardown, which surveyed 2,000 U.S. consumers who purchased counterfeit goods, nearly 1 in 3 shoppers stopped buying from the original brand after a bad counterfeit experience.
Reputation damage: Customers scammed by an impersonator often direct their frustration at the real brand through reviews, social media, and customer service. The brand bears the reputational cost of fraud it did not commit. Red Points’ research found that 44% of Millennials had their data stolen after purchasing from a fake website, and that generation is also the most likely to share negative experiences online, with 43% posting about their counterfeit experience on social media.
Customer trust erosion: Once a customer is scammed by what appeared to be your brand, rebuilding that trust is extremely difficult, even after the impersonation is removed. The same Red Points report found that 58% of unintentional counterfeit buyers were misled by trust signals such as polished website design, branded imagery, and convincing product descriptions, all of which are now easily replicated with generative AI.
Legal exposure: Depending on jurisdiction, brands may face questions about their duty of care to customers affected by impersonation, particularly if the brand was slow to act after becoming aware of the problem.
SEO and ad spend dilution: Fake websites and ads using your brand name compete directly in search results and on paid channels, driving up your cost per click and splitting your legitimate traffic. Between 2023 and 2024, Red Points detected a 179% surge in social media ads redirecting users to infringing websites across its client base, making paid channels one of the fastest-growing vectors for brand impersonation.
How do you detect brand impersonation?
Early detection is critical because impersonation campaigns can run for weeks or months before a brand discovers them.
Set up Google Alerts for your brand name and variations.
Google Alerts monitors the web for pages that mention your brand terms and sends notifications when new content appears. Set up alerts for your brand name, common misspellings, your domain name, and your key product names. This is a free starting point that catches many surface-level impersonations.
Monitor domain registrations.
New domains that closely resemble yours are a strong early signal. Use a domain management service to receive alerts when lookalike domains are registered, before they are deployed in an active campaign.
Search app stores regularly.
Search your brand name in the Apple App Store, Google Play, and major third-party stores. Any app using your name, logo, or visual identity that you did not publish is a potential impersonation.
Monitor social media platforms.
Search your brand name and logo across Instagram, Facebook, X, LinkedIn, and TikTok to identify fake accounts. Most major platforms also allow you to set up brand monitoring alerts through their business tools.
Check paid advertising.
Use Meta’s Ad Library to search for ads using your brand name. Search Google for your brand name and check whether ads appear that you did not place. Scammers often run paid ads to drive traffic to infringing sites, particularly when the fake site is not indexed in organic search results.
Check review platforms.
Negative reviews referencing products you do not sell, experiences that do not match your customer journey, or complaints about orders that were never placed with you can all signal that an impersonating store is actively operating.
How do you prevent brand impersonation attacks?
Prevention reduces the surface area available to impersonators and makes it harder for their scams to succeed even when they do launch.
Register your domains proactively.
Buy the most obvious variations of your domain name before scammers do. This includes country-code extensions (.co.uk, .de, .fr), common misspellings, and hyphenated versions. Each domain you own is one fewer that can be used against you.
Register your trademarks.
Trademark registration through the USPTO or your local IP authority gives you formal grounds to request takedowns from platforms, domain registrars, and courts. Without registration, your ability to enforce is significantly limited. Many platforms require a registration number before processing trademark complaints.
Educate your customers about your official channels.
Include clear reminders in your communications about what your official website, social media handles, and customer service contact details are. Explicitly tell customers that you will never ask for their password or payment details via unsolicited email or social media message. Customers who know what a legitimate contact from you looks like are harder to deceive.
Educate your employees.
According to the IBM Cyber Security Intelligence Index Report, human error is a contributing factor in 95% of security breaches. Regular training on how to identify phishing emails, verify unusual transfer requests through a second channel, and report suspicious activity is one of the most cost-effective prevention measures available.
Verify your accounts on social media.
Verified accounts with visible badges are harder for impersonators to replicate convincingly. Apply for verification on every major platform where your brand has a legitimate presence.
How do you report and remove brand impersonation?
The reporting process depends on where the impersonation is hosted.
Fake websites: Identify the hosting provider using a WHOIS lookup tool. If the site is hosted on a platform you recognize, such as Shopify or WordPress, file a report directly with that platform. If it uses a web host like GoDaddy, file a DMCA takedown or trademark complaint with the host. If the site appears in search results, file a separate Google DMCA request to deindex it.
Fake social media accounts: Use each platform’s intellectual property reporting tool to report impersonating accounts. Most major platforms have dedicated forms for trademark and copyright infringement. For a detailed walkthrough, see our guide on social media impersonation.
Fake mobile apps: Report infringing apps to Apple through its Intellectual Property Infringement form and to Google through the Google Play policy violation reporting tool. Include your trademark registration details and screenshots showing the similarity to your legitimate app.
Phishing emails: Report phishing emails to the Anti-Phishing Working Group at reportphishing@apwg.org and to your national cybercrime reporting body. If the phishing email uses your brand, also notify your own IT and legal team so they can issue a customer warning.
Fake ads: Report infringing ads using the platform’s ad reporting tool. On Meta, use the Ad Library to identify the ad and file through Meta’s intellectual property reporting form. On Google, report through Google’s ad complaint form. Request suspension of the advertiser account, where possible.
Domain squatting: If a scammer has registered a domain that closely resembles yours and is using it to impersonate your brand, you can file a complaint under the Uniform Domain Name Dispute Resolution Policy (UDRP). This process is managed by ICANN-accredited dispute resolution providers and is typically faster and less expensive than court action.
For business email compromise or executive impersonation targeting your employees, report to your national cybercrime authority (the FBI’s IC3 in the U.S.) and notify your email service provider to implement additional authentication controls.
How Red Points protects your brand from impersonation at scale
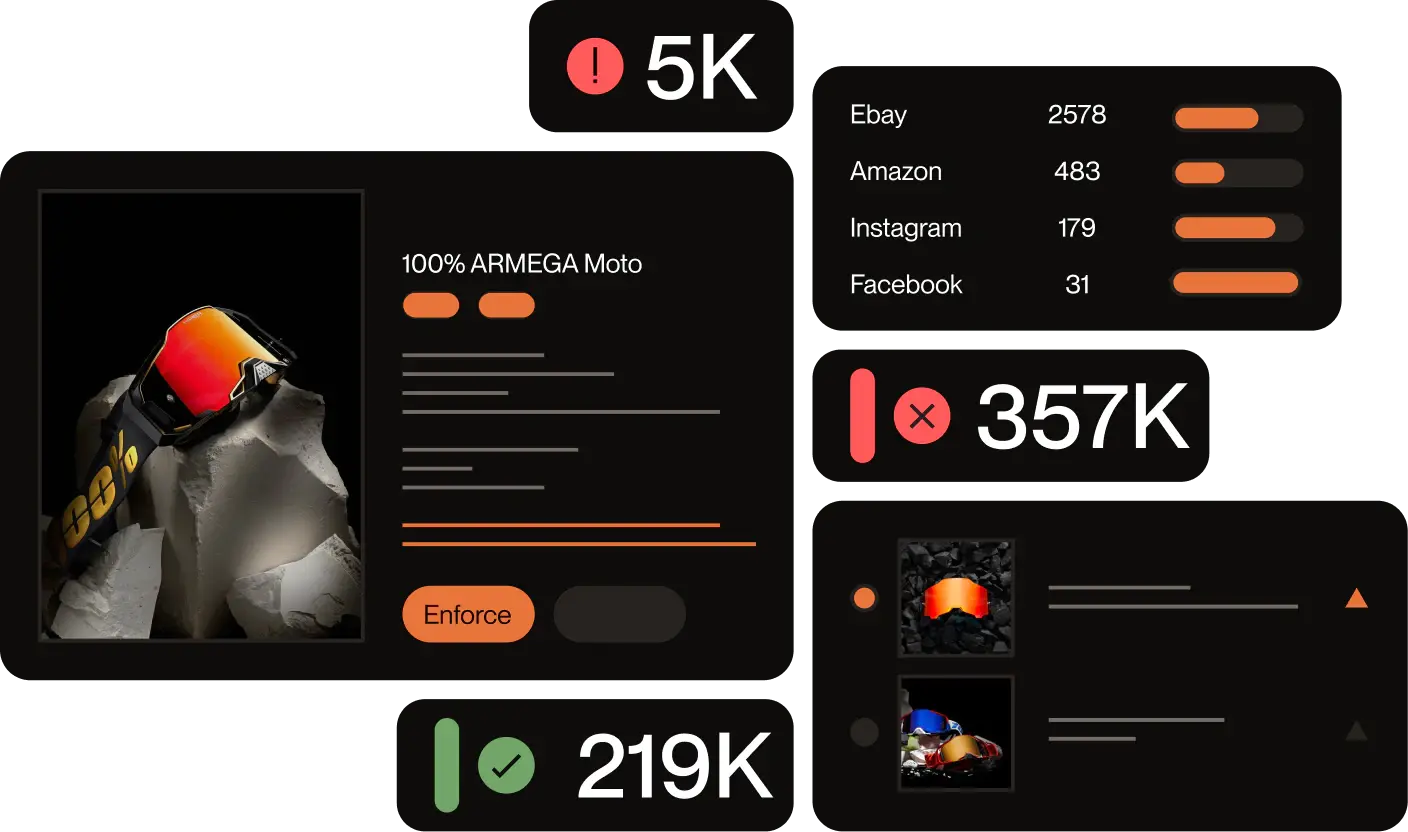
Filing individual reports works for isolated incidents. It does not work when impersonators are running dozens of fake sites simultaneously, relaunching under new domains after each takedown, or operating across multiple platforms at once. According to Red Points’ 2025 Counterfeit Buyer Teardown, standalone website infringements across Red Points’ client base jumped 59% between 2022 and 2024, with a projected further 150% increase by the end of 2026. AI tools are accelerating this trend by enabling bad actors to build convincing fake sites, rotate product listings, and relaunch after takedowns faster than any manual enforcement process can keep pace with.
Red Points’ Impersonation Removal solution monitors the open web, social media platforms, app stores, ad networks, and domain registrations continuously. Its bot-powered detection engine scans for unauthorized use of your brand name, logo, visual identity, and content, and flags new impersonation attempts as they appear rather than days or weeks later.
When an impersonation is detected, Red Points automatically collects evidence, including screenshots, HTML snapshots, and timestamps, and initiates the appropriate takedown process through the correct channel. A centralized dashboard tracks every active case, prioritizes incidents by severity, and generates reports so you can measure the volume and type of impersonation attempts over time.
For brands dealing with recurring domain spoofing, Red Points’ Domain Management solution detects newly registered lookalike domains before they are used in active campaigns. For brands whose trademarks are being misused across platforms, Red Points’ Trademark Monitoring Software provides continuous coverage across marketplaces, social media, and the web.
Request a demo to see how it works.
Frequently asked questions about brand impersonation
The terms are often used interchangeably. Brand spoofing typically refers specifically to technical methods like domain spoofing or email spoofing, where the attacker mimics a legitimate domain or sender address. Brand impersonation is the broader term covering all methods by which a scammer poses as a legitimate business, including fake websites, social media accounts, mobile apps, and phishing emails.
Phishing is a specific delivery method, typically an email or message, designed to trick recipients into clicking a malicious link or disclosing credentials. Brand impersonation is the tactic used to make phishing more convincing. Most phishing attacks use brand impersonation as their foundation because recipients believe they are hearing from a trusted brand.
Common signals include: customers contacting your support team about orders they did not place with you, negative reviews referencing products or experiences inconsistent with your business, new domains similar to yours appearing in WHOIS results, and unfamiliar social media accounts or apps using your name or logo. Setting up Google Alerts for your brand name and running regular searches across social media and app stores is a basic first step.
Yes. Depending on your jurisdiction and the nature of the impersonation, you may have grounds for action under trademark law, copyright law, anti-fraud statutes, or domain dispute policies. A registered trademark significantly strengthens your legal position. Consult a qualified intellectual property attorney before pursuing formal legal action.
In most jurisdictions, yes. Using another company’s trademark, logo, or brand identity without permission to deceive consumers constitutes trademark infringement, fraud, or both under applicable law. The FTC’s Government and Business Impersonation Rule, which came into effect in April 2024, specifically prohibits impersonating businesses and government entities in the U.S. and allows the FTC to seek civil penalties of up to $53,088 per violation.
Acknowledge the situation promptly and clearly. Issue a public notice through your official channels explaining that your brand is being impersonated and providing customers with verified ways to identify legitimate contact from you. Direct affected customers to report the scam to the FTC at ReportFraud.ftc.gov. File a takedown against the impersonating site, account, or app as quickly as possible to limit further harm.
Impersonators typically target brands that have visible online presence, recognizable logos, and a customer base worth deceiving. Brands in high-value categories such as financial services, ecommerce, technology, and luxury goods are disproportionately targeted. Growth in search visibility or social media following can trigger increased impersonation attempts as bad actors look to capitalize on a brand’s growing reputation.
Counterfeiting involves producing fake physical goods that copy a brand’s products. Brand impersonation involves misusing a brand’s digital identity, such as its name, logo, domain, or visual style, to deceive people. The two often overlap: a counterfeit seller will typically also impersonate the brand digitally to make their fake storefront appear legitimate. Both are forms of brand infringement with distinct but related legal remedies.