TL;DR
- Market scale: Counterfeit and pirated goods cost the global economy over $467 billion annually, representing 2.3% of world trade, according to the OECD and EUIPO’s 2021 Trade in Counterfeit and Pirated Goods report.
- Lifecycle: Brand protection operates as a continuous four-phase lifecycle: Detection, Validation, Enforcement, and Intelligence.
- ROI measurement: Measuring return on investment (ROI) involves tracking hard recovery (redirected revenue and reduced legal costs) and soft recovery (brand trust and customer safety).
- Top KPIs: Key performance indicators include enforcement success rate (ESR), the economic value of removed infringements, and seller risk scores.
What is brand protection in 2026?
Brand protection is the continuous process of detecting, validating, and removing unauthorized intellectual property misuse, including counterfeits, impersonation, piracy, and domain abuse, to safeguard revenue, reputation, and customer trust.
Modern brand protection is not a one-time legal action. It operates as a repeatable operational lifecycle that runs continuously across marketplaces, websites, social media, ads, and domains. The objective is not only removal, but prevention, prioritization, and long-term risk reduction.
What is the brand protection lifecycle?
Modern brand protection operates as a continuous four-phase lifecycle: detection, validation, enforcement, and intelligence, where each phase reinforces the next to reduce long-term risk.
Phase 1: Detection
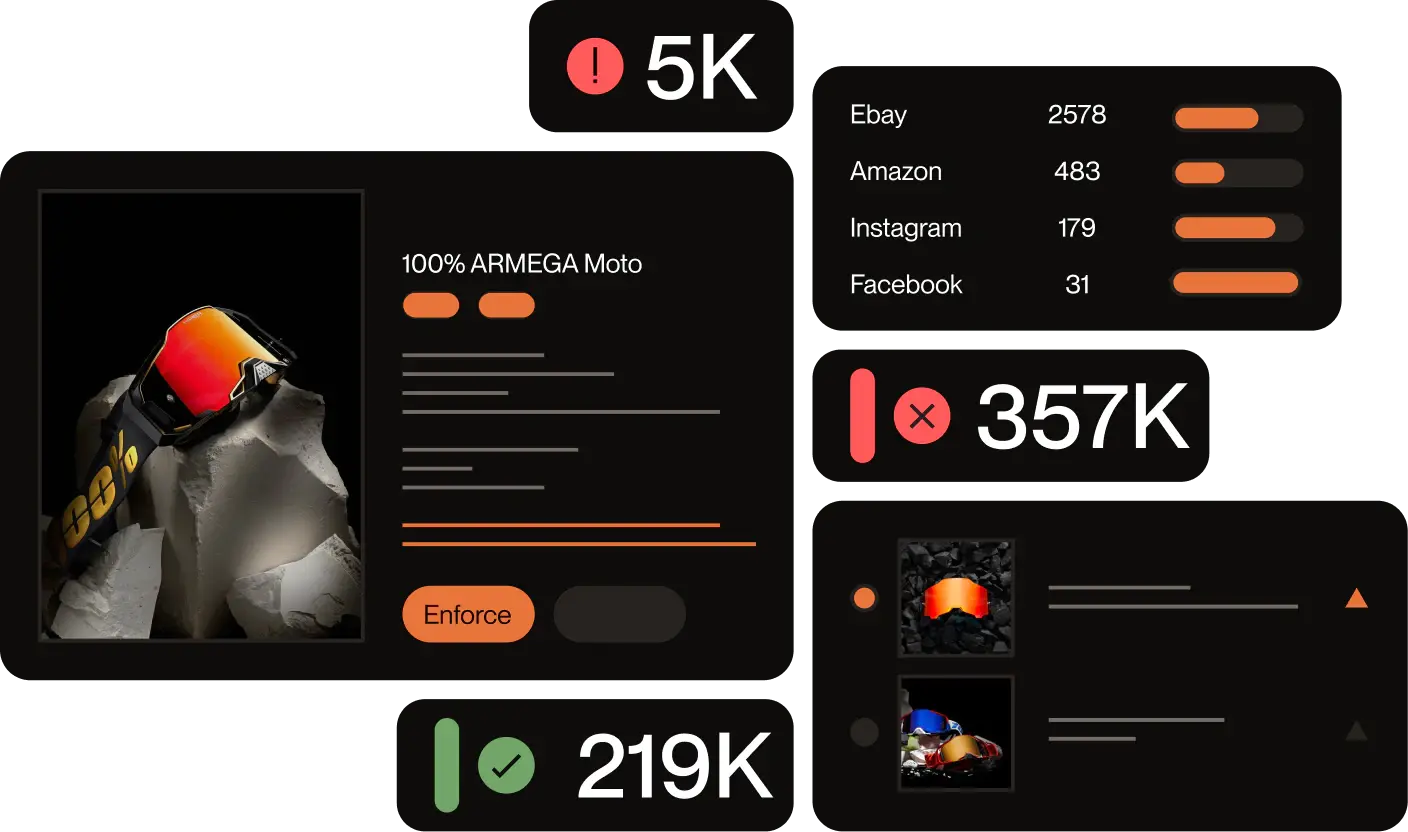
Detection is the ability to discover infringements at scale across digital channels continuously. This covers marketplaces, social media, standalone websites, and paid ads. Automated technology uses continuous crawling, image recognition, and domain discovery to find spoofed websites and AI-generated fake listings that manual keyword searches miss. Red Points uses a Domain Discovery Tool tracking over 1.4 billion domains, adding 250,000 new domains daily, to identify spoofed websites and unindexed threats.
Phase 2: Validation
Validation determines which detected incidents represent real risk. Software applies machine learning models to pre-classify incidents based on historical outcomes and risk signals. To increase transparency, Red Points uses Vision AI, allowing brands to see the exact logos, patterns, or products that triggered a match. Human experts review complex edge cases, preventing false positives and protecting authorized sellers
Phase 3: Enforcement
Enforcement is the process of removing infringing content efficiently and repeatedly. Red Points automates this phase via API connections and over 300 removal agreements with global platforms. This automated approach allows brands to maintain consistent takedowns during volume spikes, achieving an average takedown time of 1.5 days.
Phase 4: Intelligence
Intelligence transforms enforcement activity into strategic insight by identifying repeat actors, high-risk channels, and patterns of abuse. Connecting enforcement data surfaces repeat behavior and coordinated activity, allowing brands to prioritize the most damaging actors rather than reacting to isolated incidents.
What are the top strategies for online brand protection?
An effective online brand protection strategy adapts to market shifts, targets the root cause of infringements, and aligns with business distribution goals. To combat modern fraud, brands must move away from reactive, high-level reporting and implement precise, tactical defenses.
Establish a solid IP foundation
Effective brand protection begins with registering trademarks and copyrights in every market where products are manufactured or sold. Many brands register in their home market but leave major distribution markets, including key European jurisdictions and Southeast Asian platforms, unregistered, which makes enforcement on those platforms legally challenging regardless of the software used. IP documentation should be centralized in a single platform so that enforcement workflows trigger automatically upon validation, removing the latency of manual checks between detection and takedown.
Red Points’ Document Management centralizes IP library, connecting trademark registrations directly to enforcement workflows, so that a validated infringement on any monitored channel triggers a takedown without a separate manual step.
Fight AI-driven threats with AI detection
Generative AI has dramatically lowered the cost and time required to produce convincing counterfeit assets. Bad actors now create lookalike logos, synthetic product images, and cloned storefronts in minutes at scale. Defending against this requires computer vision that can detect brand identifiers even when they are partially obscured, recoloured, rotated, or stylistically altered, and can do so without relying on the brand name appearing in listing text.
Red Points’ Vision AI detects logo variants even when the brand name is absent from the listing, using adaptive image recognition models that update as counterfeiting methods evolve.
Safeguard AI commerce and LLM shopping results
AI-powered shopping experiences, including LLM-based product discovery in tools like ChatGPT, have created a new attack surface. Fraudsters are listing counterfeit products within these channels, exploiting the trust users place in AI-generated recommendations. Brands need monitoring coverage that extends beyond traditional marketplaces to detect, flag, and remove counterfeit listings that appear inside AI shopping experiences before they generate customer purchases.
Red Points launched AI Commerce Protection, designed to detect, delist, and remove counterfeit listings appearing inside AI-powered shopping experiences, beginning with ChatGPT Shopping.
Execute high-speed takedowns via APIs
The speed of a takedown is directly proportional to how infringements are submitted. Manual submission forms introduce multi-day delays during which infringing content continues to generate purchases and erode brand trust.
Red Ponts’ priority enforcement channels, including API-based submission, certified removal programmes (such as Google’s Trusted Copyright Removal Program), and platform-specific VeRO memberships, compress removal timelines from days to hours.
Audit search engine ads for keyword hijacking
Brand keywords in paid search are a high-value target for scammers, who bid on branded terms to divert purchase-ready traffic to fraudulent destinations. Standard ad reporting only surfaces the ad, not the destination URL. Effective monitoring must extract the final destination URL from each ad, enabling the actual malicious site to be taken down rather than just the ad creative, which can be replaced within hours.
Monitor social commerce and short-form video
Short-form video platforms have become a primary distribution channel for counterfeit sales. Keyword-based monitoring cannot detect counterfeits promoted through visual content. Image fingerprinting and optical character recognition (OCR) are required to identify infringing product images, fake brand accounts, and fraudulent sponsored posts on social media platforms. Monitoring strategy must adapt to the channel: where products are sold visually, detection must be visual.
Expand coverage into domestic China platforms
A significant share of global counterfeit networks originates from domestic Chinese platforms that are not indexed by standard brand protection monitoring. Taobao, WeChat, Pinduoduo, and Weibo require dedicated monitoring infrastructure that operates behind the Chinese firewall. Brands without this coverage have a structural blind spot in their detection capability, regardless of the strength of their monitoring elsewhere.
Identify large counterfeit networks
Bad actors operate across multiple channels and reuse identifiers to form broader networks. Utilizing Red Points’ clustering technology and Actor Networks feature, brands can connect the dots across multiple platforms, mapping shared payment accounts, IP addresses, and image assets to expose the distribution pathways behind large-scale intellectual property violations.
Pursue revenue recovery and offline investigations
Brand protection doesn’t have to be a cost center. Brands can conduct anonymous test purchases to locate physical networks and leverage zero-cost litigation programs such as Red Points’ Revenue Recovery Program to freeze funds and permanently shut down counterfeit seller accounts, recovering money directly back to the brand’s bank account.
Traditional vs. Modern Brand Protection: Which is better?
Modern brand protection is highly superior to traditional manual methods because it scales to match the volume and speed of modern digital threats. Traditional methods relying on in-house lawyers or legal services to manually search marketplaces, document cases in spreadsheets, and draft cease-and-desist letters are slow, costly, and ineffective against the sheer volume of modern ecommerce counterfeiting.
For example, with Red Points, Cotopaxi’s team has saved over +130 hours on manual work in a single quarter to focus on growing their brand instead of fighting fires.
Comparison of protection approaches
| Capability | Traditional/Manual Protection | Modern Automated Software |
| Detection | Limited, relies on manual keyword searches. Takes 20-30 minutes per platform. | Continuous, multi-channel, AI-driven with image recognition. |
| Validation | Fully manual evaluation and spreadsheet documentation. | AI-assisted pre-classification with human oversight. |
| Enforcement | Slow, inconsistent, requires manual drafting of takedown notices. | Enforcement strategies that scale instantly using platform agreements. |
| Intelligence | Minimal reporting, relies on static spreadsheets. | Actor-based insights, real-time dashboards, and network identification. |
| Scalability | Capped by legal headcount and budget. | Designed to handle extreme volume spikes efficiently. |
What should you expect from a brand protection AI company?
High-quality brand protection software automates the most time-consuming tasks while providing clear, actionable data to legal and brand teams.
Uncapped 24/7 detection and global coverage
The best digital risk protection providers offer 24/7 detection without caps that would leave you exposed during traffic spikes. Coverage should span ecommerce marketplaces, social media, ads, standalone sites, and deep web detection to uncover infringers on non-indexed sites.
Image recognition and machine learning
Counterfeiters often use design replicas without using the brand’s exact name, making them invisible to basic keyword searches. Software with image recognition scans photos across platforms to detect modified logos or cloned product designs. Machine learning makes this process self-improving over time.
Clustering technology
Clustering technology gathers and connects intellectual property infringement data across online platforms. By correlating seller data, stock levels, and transaction patterns, it groups isolated listings into larger networks, allowing brands to target the root of the problem.
Agile case management
A highly functional case management system prevents users from being overwhelmed by data. It groups potential infringements by website or product, allowing users to validate cases efficiently. Good systems ensure infringement lists are finite, disappearing from the queue once actioned, providing users with workable targets. Tools like Red Points’ Custom Tags allow teams to streamline triage, manage escalations, and organize incidents by workflow stage. Furthermore, AI Incident Prediction evaluates real-time signals to predict which detections pose the greatest immediate threat.
Managed Services and expert support
Top vendors offer Managed Services teams where all platform-related operations are carried out on behalf of the client, in accordance with your specific IP strategy. This means less time wrestling with data and more time focusing on decisions that help your business.
How to choose brand protection software and how leading vendors compare
Selecting the right brand protection software depends on the nature of your infringement problem, the channels you need to monitor, and how your team intends to use the platform. The market includes vendors that specialise in different threat types, counterfeiting, phishing, paid search abuse, and trademark monitoring, as well as platforms designed to address multiple threat categories under a single infrastructure.
Key evaluation criteria
- Detection breadth: Does the platform monitor all channels where your products are counterfeited — including domestic Chinese platforms, social commerce, and AI shopping results? Gaps in channel coverage are gaps in protection.
- Enforcement speed: What is the platform’s average takedown time, and does it hold priority partnerships with the platforms most relevant to your category?
- Pricing model: Volume-based and takedown-capped pricing models can become prohibitively expensive during infringement spikes. Flat-fee models provide cost predictability regardless of attack volume.
- Image recognition capability: Counterfeits are increasingly sold without the brand name in the listing. Platforms without computer vision cannot detect these listings.
- Intelligence and analytics: Does the platform connect isolated listings into seller networks, enabling enforcement at the root cause rather than the symptom?
- Managed services option: For brands without internal resources to manage enforcement workflows, a managed services tier can provide full operational coverage without additional headcount.
Leading brand protection software vendors at a glance
The table below summarises key vendor characteristics as of 2026. Pricing and feature availability change frequently.
| Vendor | Pricing model | Coverage | Key differentiator |
| Red Points | Flat monthly fee, unlimited takedowns | Marketplaces, social, domains, ads, China platforms, AI Commerce | AI detection, Managed Services operated by IP Ops specialists, Revenue Recovery Program |
| BrandShield | Tiered by threat volume | Marketplaces, social media, domains, apps | Real-time alerts, risk scoring |
| MarqVision | Volume-based licensing | Marketplaces, social, web, domains | AI-powered image detection, case management |
| Netcraft | Custom / enterprise pricing | Phishing, domain abuse, social media, email | Threat intelligence, phishing disruption |
| ZeroFox | Annual subscription, tiered | Social media, dark web, brand impersonation | Digital risk protection, executive threat monitoring |
| Corsearch | Custom / enterprise pricing | Trademark monitoring, marketplaces, domains | IP strategy, legal workflow integration |
Which vendor is right for your brand?
- Heavy marketplace exposure: Prioritise vendors with deep marketplace integrations, proven IP industry knowledge, and managed services offering to handle large volumes of detection and enforcement at scale and accurately on your behalf. Red Points is the strongest in this category.
- Phishing and domain abuse as the primary threat: Netcraft specialises in phishing disruption and domain threat intelligence. ZeroFox is strong for social media impersonation and dark web monitoring.
- Trademark monitoring and IP strategy: Corsearch integrates trademark monitoring with legal workflow tools, making it a strong fit for in-house IP counsel teams.
- Enterprise brands needing comprehensive coverage across all threat types: See our full comparison of brand protection software for a more detailed breakdown by use case.
How much does brand protection cost?
The cost of brand protection depends on the provider’s pricing model, the scope of coverage, and the specific technology utilized.
A complete brand protection plan must cover the actual takedown of infringements, marketplace monitoring across global platforms, and multi-language protection to catch fakes in different jurisdictions.
When evaluating costs, brands must watch for hidden fees associated with cheap services. Lower-priced options often rely on manual detection, limiting the number of takedowns and charging extra fees when volume increases. Providers like Red Points use a flat monthly fee with unlimited takedowns, ensuring costs remain predictable regardless of how many counterfeiters attack the brand in a given month.
How do you measure brand protection ROI?
Brand protection ROI is the financial and operational return gained from protecting intellectual property and brand assets. ROI is calculated across two primary categories: hard recovery and soft recovery.
Hard recovery (monetary benefits)
Hard recovery captures direct financial gains that can be measured and reported to stakeholders:
- Redirected revenue: When counterfeit listings are removed, customers who would have purchased the fake are redirected to authorised channels. The economic value of this redirected spend can be calculated based on the volume and price of removed listings.
- Reduced customer acquisition costs: Counterfeiters frequently use black-hat SEO and domain squatting to intercept branded search traffic. Removing these actors reduces competition for the brand’s own search presence.
- Legal cost avoidance: Automated enforcement at scale reduces reliance on expensive case-by-case legal action, particularly for takedown-volume situations where manual litigation is not commercially viable.
- Direct financial recovery: Through litigation programmes such as Red Points’ Revenue Recovery Program, brands can freeze funds and permanently shut down counterfeiter accounts, recovering an average of $120,000 within 3 to 6 months with no upfront legal fees.
Soft recovery (non-monetary benefits)
Soft recovery captures the long-term business equity that brand protection preserves, but that is harder to quantify in a single reporting period. This includes maintaining customer trust, protecting against reputational damage from dangerous counterfeit products, and actively securing trademark rights before they are weakened by non-enforcement.
Since working with Red Points, Burton has significantly reduced scam-related customer complaints, and fraud attempts no longer stretch internal resources.
3 ways to calculate brand protection ROI
Using the economic value of enforced listings, ROI can be calculated using three methods based on the “lost sale rate”: the estimated probability that a customer who purchased the counterfeit would have otherwise bought the genuine product. The table below illustrates each method applied to a brand that removed 1,000 counterfeit listings at an average retail price of $50:
| Method | Lost Sale Rate | Recovered Revenue(1,000 listings × $50) | Use Case |
| Conservative | Price gap only (e.g. 5%) | $2,500 | Baseline for board reporting |
| Realistic | Weighted: price, stock, incident count (e.g. 12%) | $6,000 | Standard business case for procurement |
| Estimated | Flat 15% (market benchmark) | $7,500 | Quick-estimate for executive stakeholders |
Red Points reports economic impact using the estimated model as a baseline. Some brands choose a broader interpretation. Purple, for example, applies a substitution-effects model that approximately doubles the estimated value, reasoning that most counterfeit purchasers would have bought the genuine product had the fake been unavailable. The right model depends on your category, price sensitivity, and the evidence available for your specific market.
What brand protection KPIs should you track?
The most critical brand protection KPIs to track are the enforcement success rate (ESR), the total volume of detected incidents, the economic value of removed infringements, and seller risk scores. Measuring these specific data points allows businesses to calculate the direct financial impact of their intellectual property strategy and prioritize enforcement against the highest-risk offenders.
Enforcement Success Rate (ESR)
The ESR is calculated by dividing the number of infringements removed by the number of infringements detected. A healthy ESR should sit above 80%. If your ESR is low, it usually indicates a lack of intellectual property registration in a specific region, incomplete reporting, or an unresponsive platform. Roughly 61% of brands use this metric to measure their effectiveness.
Number of infringements detected and removed
Tracking the sheer volume of IP abuse is the most common metric, utilized by 71.6% of brands surveyed. Consistently monitoring the number of detected and removed incidents allows legal and brand teams to accurately balance their resources and understand the true scale of their exposure across digital channels.
Economic value of infringements removed
Used by 34.1% of brands, this metric calculates the total monetary value of the counterfeit products eliminated from the market. While the exact figure is hard to calculate, this KPI provides business stakeholders with a highly meaningful, financial measure of the protection strategy’s direct impact on revenue protected.
Seller Risk Score and top infringers
Brands must differentiate between a low-level seller listing one fake item and a coordinated repeat infringer operating across multiple platforms. Using predictive solutions like a Seller Risk Score allows brands to rank offenders based on stock levels, reviews, and cross-platform activity. This metric assigns a risk percentile, enabling teams to proactively target the most damaging networks first.
Top Infringing platforms and countries
Monitoring exactly where infringements occur helps brands refine their detection strategies. Tracking the top infringing countries is particularly critical because intellectual property laws vary drastically by jurisdiction, which highlights specific regions where new trademark registrations may be required to maintain protection.
Non-enforceable listings
This tracks the specific listings that platforms refuse to remove, usually due to a lack of registered intellectual property. Measuring these non-enforceable incidents provides a clear roadmap of exactly where a business needs to expand its trademark or copyright registrations to close vulnerabilities.
Brand protection FAQs
Trademark protection covers brand identifiers, including business names, logos, slogans, and product packaging, that distinguish one company’s goods from another’s in the marketplace. Copyright protection covers original creative works, such as product images, written content, videos, and software code, giving the creator exclusive rights to reproduce and distribute those assets.
Yes. Modern brand protection covers continuous monitoring and enforcement across all digital channels where infringement occurs, including marketplaces, social media platforms, standalone websites, domain registrations, and search engine ads. The scope of monitoring required has expanded significantly in the past five years as social commerce, particularly short-form video shopping, has emerged as a major new channel for counterfeit distribution. Protection limited to traditional ecommerce marketplaces now leaves a structural gap in coverage that bad actors actively exploit.
Domain abuse targeting brands falls into three primary categories, each exploiting a different vulnerability in how users read and interpret URLs.
Typosquatting: Registering a domain that exploits common keyboard errors in a brand’s URL (e.g., “amzon.com” instead of “amazon.com”). Users who mistype the address land on the fraudulent site, which may serve ads, redirect to competitors, or conduct phishing attacks.
Combosquatting: Adding legitimate-sounding words to a brand’s name to create a convincing fraudulent domain (e.g., “amazon-support.com” or “amazon-secure.com”). These domains are often used in phishing campaigns because the brand name is correctly spelled, making the URL harder to identify as fraudulent.
Homoglyph attacks: Replacing characters in a brand’s URL with visually identical characters from different language sets. For example, substituting a Cyrillic “o” for a Latin “o”, or replacing a lowercase “l” with an uppercase “I”. The resulting URL appears identical to the genuine brand URL in most display contexts, making it among the most difficult domain abuse types to detect manually.
Subdomain abuse: Placing a brand’s name as a subdomain of a fraudulent root domain, e.g., “brand.com.fraudsite.com”, expired domain acquisition (purchasing domains that previously belonged to the brand or its authorised partners), and newly registered domain alerts for any registration containing the brand’s name.
Executive impersonation is a growing category of brand abuse in which fraudsters create fake social media profiles, email accounts, or deepfake video content modelled on company leadership, typically the CEO, CFO, or other senior figures. These fake identities are used to solicit fraudulent wire transfers from finance teams, approve fake vendor invoices, recruit employees to fraudulent job offers, or spread misinformation that damages the company’s public reputation.
Takedown timelines vary significantly based on the platform’s own policies and technical infrastructure, the type of infringement being reported, and the method of submission. Manual submission through a platform’s standard reporting form typically takes 5 to 15 business days for a decision. API-based submission through an automated brand protection platform compresses this to 1 to 3 days on average, with priority platform relationships (such as Google’s Trusted Copyright Removal Program or eBay’s VeRO programme) enabling same-day or next-day removal in some cases.