Social media is an indispensable tool for ecommerce and brand owners to promote their products and communicate with their audience. However, brands can only reap the benefits of social media for business when they protect their accounts from various attacks. Hackers, scammers, and impersonators are an ever-growing threat on social media.
In this article, you will learn how to secure your social media for business efficiently and stay ahead of potential attacks. We provide an overview of the most common threats on social media and walk you through concrete actions you can implement.
What are the threats brands are facing on social media?
Scammers
Crypto scams
Popular fraud involves crypto scams where infringers promote cryptocurrency giveaways on various social media platforms. By doing so, a scammer pretends to be a celebrity or trusted entity from the crypto community that hosts a giveaway.
In order to participate in the giveaway, users are asked to send a certain amount of cryptocurrency to a giveaway address to verify their wallet address. Scammers make users believe that in turn, they receive their giveaway. The catch here is that because crypto transactions can’t be withdrawn, users can’t get their money back after sending money to a scammer’s address.
Phishing attacks
Another common scam is phishing attacks that lure customers with fake coupons for popular brands. To claim the coupon, users have to hand over personal information like their names, addresses, date of birth or even bank details. This type of scam often takes place on Facebook.
Ad scams
Scam ads are a growing problem on Facebook and Instagram. Infringers use fake ads to make consumers believe that they are buying from a legitimate brand. They usually lure shoppers with very cheap prices for certain products or services.
Scammers use images or other identifying information from the real brand to make it look real. When unknowing shoppers fall for the fake ad and make a purchase, they either receive a low-quality knock-off product or no product at all. This often leads to reputational damages for brands as customers leave bad reviews on the original brand.
Impersonators
Creating a fake social media account is one of the easiest tasks for infringers. This form of business identity theft involves the use of names, images, logos, or other identifying information of persons and brands for malicious purposes. Fake accounts are used to target customers with aggressive fake advertising campaign attacks, sell counterfeit products or steal sensitive information.
It is important to know that impersonators don’t limit themselves to fake social media accounts. By copying identifying information through copyright infringement or trademark infringement, they also create look-alike websites, fake apps, phishing emails and other crimes.
Hackers
Hackers are the burglars of the internet. They break into devices mainly with the goal to steal, alter or delete information which can cause huge financial and reputational damages for brand owners. After gaining access to social media accounts, hackers often use the accounts to distribute malware that steals sensitive data like login credentials or other information from users.
Social media is attractive for hackers because of the various options to distribute malicious codes. These include malvertising, shared images and links, plugins and other digital media. The fact that billions of people around the globe use and share content on social media reinforces the problem.
Instagram appears to be the social media platform that is especially prone to be hacked on mobile phones.
What are the ways of protecting your social media accounts?
Choose individual strong passwords
Passwords are often the biggest security gap and the easiest to fix. A password of 8 lowercase letters makes up 209 billion possible combinations which might sound a lot, but a computer is able to crack this instantly. To be secure, the passwords for your social media accounts should be at least 12 characters long and contain a random combination of capital and lowercase letters, numbers and symbols.
Make sure not to use the same password for different social media accounts. Also, although Facebook allows you to sign in to other social media accounts with your Facebook account, you should avoid signing in to multiple accounts with the same account. Lastly, you should renew your passwords periodically to increase security.
Use two-factor authentication
Enabling two-factor authentification is one of the most effective ways of shielding your business social media accounts from hackers. It confirms the user’s identity by using a combination of a password and a confirmation code sent to the account owner via an app, email or text message. While this login process is slightly more complicated than just using a password, it adds an extra level of protection to your social media accounts and effectively protects your data.
Avoid public Wi-Fi connections
Public Wi-Fi networks have a number of security gaps that make them too risky for managing your business social media accounts. Hackers can create fake “guest Wi-Fi” networks for public spaces like cafes. As soon as you connect to such a network, bad actors can access your information and work. But also legitimate public Wi-Fi connections at airports, libraries and other places don’t meet the security standards that are needed to keep your social media accounts for business safe.
Keep track of who has access to accounts
When it comes to managing your social media accounts for business the saying “too many cooks spoil the broth” holds true. It happens quickly to lose sight over who has access to accounts that are posting content. Limiting the number of people who have access helps reduce the risk of your social media accounts being hacked through emails, mobile phones or computers.
Implement a social media policy
Clear guidelines and practices on how to use social media for your business outline the safe use of social media and make it easier for your employees to follow them. A social media policy helps prevent security threats and inappropriate posts from employees. It should include guidelines for copyrights, communication, brand voice and confidentiality.
Create a separate email address for your social media
The advantage of using an email address exclusively for your social media is that it protects other sensitive data in case your account gets compromised. If you use an employee’s address, a hacker could also get access to other confidential information which would worsen the problem. Make sure to use a strong password that you only use for this email address.
Monitor your accounts and potential threats
Keep an eye on all your social media accounts including the ones that you signed up for but not using. These are the ones that are especially prone to hackers. You should frequently check the posts on all accounts. A post that seems suspicious or that deviates from your guidelines and content plan could be a sign of a compromised account.
What’s next
Impersonators that mimic your brand for fraudulent purposes on social media can lead to revenue losses, stolen customer data and reputation damages. That’s why it is important to take protective measures that shield your social media accounts for business from various attacks.
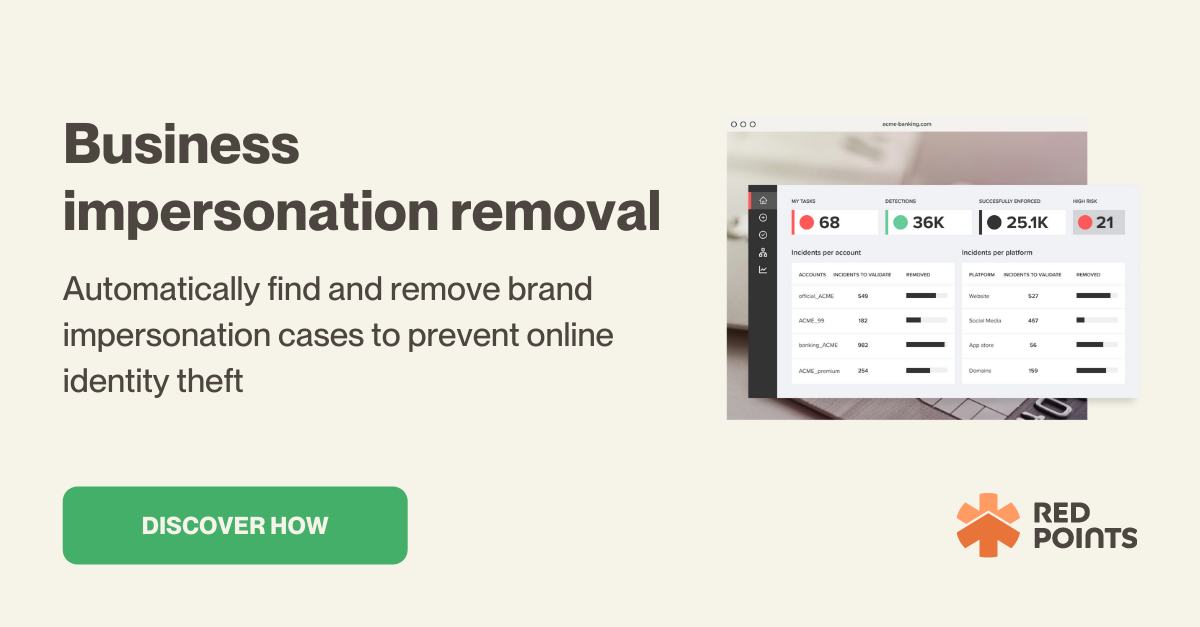
Red Points is specialized in safeguarding your brand on social media. Our software detects social media infringements across platforms and requests takedowns automatically.
Reach out to us today to protect your brand on social media.