Table of Contents:
Last updated on: August 17, 2022
Over the past year, business identity theft has increased dramatically. Criminals carry out impersonation attacks on companies to illegally make a profit on the brands’ success, leaving businesses affected with damaging repercussions.
Data from PwC revealed that 47% of companies worldwide have experienced fraud in the past 24 months.
It is, therefore, more than ever indispensable for business owners to take immediate action when facing any form of corporate identity theft. In this article, we show you the different types of business identity theft, its consequences on businesses, and what can be done against it.
Business identity theft, also known as corporate identity theft is the illegal impersonation of a business. In that sense, the victim can be any type of entity with a business Tax ID, from an individual proprietorship to a large corporation.
The tactics fraudsters use to steal business identity information and use it to make a profit vary in form as we outline here:
Infringers create fake accounts that use the names, images, logos, or other identifying information of persons, brands, and companies for deceitful purposes. It can take a few days until such newly created accounts are detectable. Impersonators disguised with stolen identities exploit these timeframes of less visibility to target customers with aggressive fake advertising campaign attacks.
Another technique impersonators often use is copying the entire design of established company websites. Unaware customers are led to these fraudulent websites through search engines, social media ad campaigns, or emails.
One of the common examples of business identity theft is implementing a brand’s logo or name in emails sent by impersonators to employees. By doing so, fraudsters seek to get a company’s banking information. This type of information can be used for financial frauds like obtaining loans, credit lines or credit cards in the company’s name.
It is very simple for thieves to get the information they want. Some information may even be available online for free if companies publish documents that contain corporate information like sales tax numbers or business license numbers. Business identity thieves use stolen company information to file fraudulent tax returns for a refund.
Criminals might also steal your business name or logo and register it as an official trademark. In the aftermath, they claim a ransom for releasing the trademarked business identity.
Business infringers might issue fake invoices with your company identity or impersonate your business partner by sending an invoice in their name and asking you for payment.
We have stated that identity theft can impact any type of business. It has the potential to harm a brand’s reputation and in turn, significantly undercut a business’ margin. Here below are the most hard-hitting repercussions for businesses:
The reputation of your business is one of the most important and fragile assets. It defines the quality of your relationships with creditors, business partners, and most importantly, your customers. Being targeted by business and corporate identity thieves can dramatically change the way your company is perceived and break the trust you had built with your customers.
Customers that have fallen into the trap of fake websites may end up buying fake products or never receive the products that they paid for. The same applies to fake social media accounts. Customers are left deflated from their experience and decide to opt for another brand next time.
Significant income losses pose a major risk, especially for small businesses that don’t have large financial reserves. Business owners might be struggling to pay employees, partners, vendors or capital providers on time. The same goes for upholding tax obligations or the purchase of supplies.
The problem of lost revenues has seen a dramatic increase in the recent past. Data from the UK shows that brand impersonations have almost doubled in the first half of 2020. 15.000 reported cases (a 84% increase compared to 2019) have caused £58 million losses to impersonation scams.
If your business identity has been used for filing fraudulent tax returns, it is likely that you will be confronted with tax penalties and audits. Clarifying the circumstances can be costly and tedious.
Thousands of companies are victims of business identity theft, and the most important thing to do is to take action immediately.
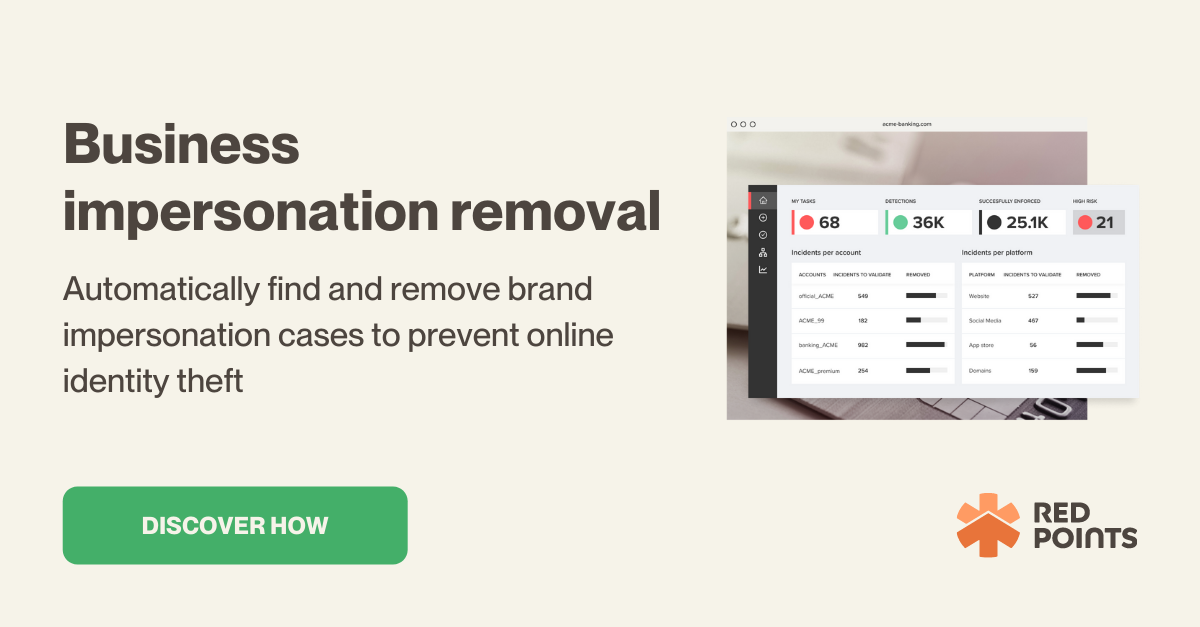
Red Points impersonation protection and removal software help you with any kind of digital identity abuse. It automatically detects and removes fake websites, domains, social media accounts, and apps to protect your clients and business from identity theft.
Get in touch with us to learn more about how we can help you with business identity theft solutions tailored to your needs.