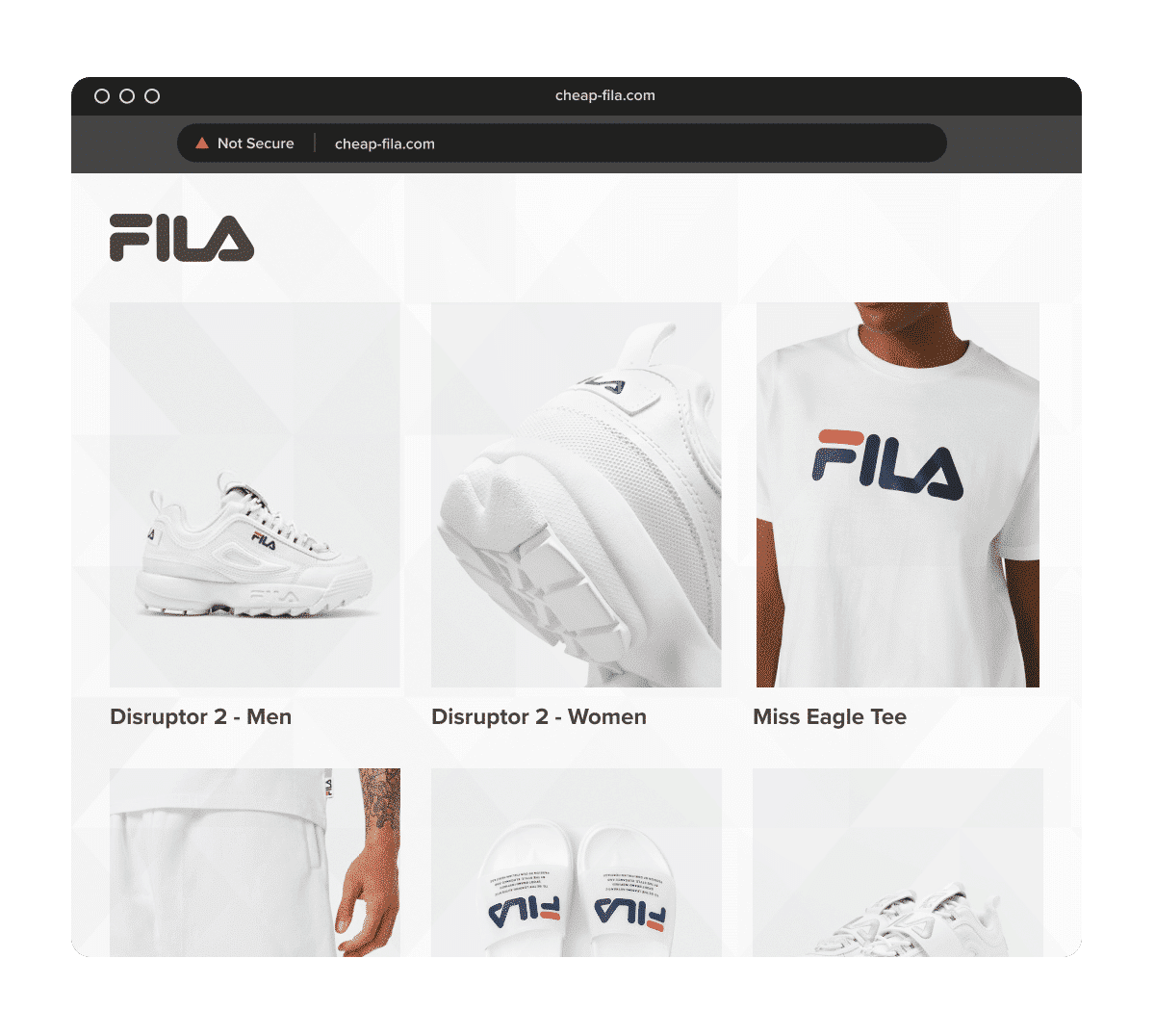
A customer clicks an ad on Facebook, Instagram, or Google, lands on what looks exactly like your storefront, places an order, and never receives the product. The logo is yours. The images are yours. The product descriptions are yours. The only thing that is not yours is the website.
That is website cloning. And for brands, the damage goes far beyond one fake page. Clone sites can steal revenue, capture payment data, trigger chargebacks, flood support teams, and erode trust with customers and distributors.
TL;DR – Key takeaways
- Website cloning happens when attackers copy your storefront’s design, branding, product pages, images, or checkout flow to impersonate your business.
- A cloned website is not always the same as a generic fake website. The defining feature is replication – the scam works because the site looks convincingly like yours.
- The biggest business risks are revenue (diversion, customer fraud, support costs, brand erosion, and payment-data theft.
- The strongest defense is not one tactic. Brands need legal coverage, technical hardening, image protection, domain monitoring, backlink monitoring, ad monitoring, and fast enforcement.
- Manual checks help as a baseline, but they do not scale across search engines, domain databases, social media, marketplaces, and paid ads.
- Once a clone is confirmed, enforcement must run in parallel across the hosting provider, search engines, paid ads, social media, and the domain registrar. Sequential filing gives operators time to relaunch before each channel is cleared.
Website cloning vs fake websites
Website cloning and fake websites are closely related, but they are not the same thing.
A cloned website is a specific type of fake website built by copying a real brand’s look and feel. The scam works because the site closely replicates your homepage, product pages, images, branding, navigation, and sometimes even your checkout flow. In other words, the core tactic is imitation through replication.
A fake website is the broader category. It covers any site that impersonates your brand, misleads customers, or uses your IP without authorization. Some fake websites are cloned versions of real stores. Others are much simpler. They may use your logo, product names, or brand language without copying your full site structure.
That distinction matters because the response is different. If the issue is website cloning, brands need to understand how their content is being copied, which brand assets are being reused, whether traffic is being pushed through ads or social media, and how to detect similar clone sites early. If the issue is a fake website, the priority is usually enforcement – reporting the site, identifying the host or registrar, deindexing pages, and removing related ads or accounts.
Here is the simplest way to think about it:
| Term | What it means | What matters most |
| Website cloning | A scam site that copies and replicates your real website to look legitimate | Detection, prevention, monitoring copied assets, and incident response |
| Fake website | Any unauthorized site that impersonates your brand or misleads customers | Takedown, reporting, deindexing, and enforcement |
So while every cloned website is a fake website, not every fake website is a cloned website.
That is why this article focuses on how clone sites are built, how to spot the warning signs, and how to reduce the risk before customers are exposed. If you think your brand is dealing with fake websites, check out our separate fake website guide.
So, what is website cloning?
Website cloning is the unauthorized copying of a legitimate site’s visual design, structure, text, images, product catalog, and sometimes code in order to impersonate the original brand.
Clone sites are typically built to do one or more of the following:
- Steal card and customer data
- Sell counterfeit products
- Take payment and never ship anything
- Divert traffic away from your official site
- Run short-term scam campaigns through ads and social media
In practice, cloned websites usually imitate the parts of your site that create trust fastest: your homepage, hero banners, product images, reviews, navigation, logo placement, brand colors, FAQs, and checkout flow.
Why website cloning is so damaging
Clone sites are effective because they exploit brand familiarity. A survey conducted by Red Points shows that realistic product photos, official-looking branding, and clean product descriptions are some of the top reasons shoppers trust fake listings unintentionally.
That creates five immediate business problems.
1. Revenue is diverted before you see the problem
A cloned site can intercept demand from branded search, paid social campaigns, affiliate traffic, and word of mouth. By the time your team notices the issue, real purchase intent may already have been diverted.
2. Customers blame the brand, not the scammer
Customers do not usually distinguish between your official store and a convincing clone. When they get scammed, your support, reviews, and reputation absorb the impact.
3. Fraud exposure can spread across channels
Website cloning rarely stays on one domain. Attackers often connect cloned sites with Google Ads, Meta ads, Facebook pages, Instagram accounts, TikTok content, and marketplace listings to create a full acquisition funnel.
4. Your team loses time to manual investigation
Legal, ecommerce, trust and safety, and customer support teams often end up chasing screenshots, domain records, and ad reports one by one.
5. Clones can reappear fast
Even after one site is removed, the same operator can relaunch with a new domain, new ad account, new proxy service, or a slightly changed page structure.
How cloned websites are built
Not every clone is technically sophisticated. Many are assembled quickly using widely available tools.
Common cloning methods include:
- Content scraping – copying your HTML, text, product data, or image library
- Image theft – reusing official product photos, banners, and logos
- Template mirroring – recreating the same layout and UX patterns without copying the full codebase
- Dynamic scraping – repeatedly pulling fresh changes from the original site
- Ad-to-clone routing – using paid ads or social posts to send traffic to the clone
- Typosquatting or lookalike domains – registering domains that resemble your brand name
This is why cloned sites often look unusually complete. They do not need to invent trust from scratch. They borrow it from you.
9 warning signs your website has been cloned
Brands often spot clones too late because they wait for a customer complaint. A stronger approach is to monitor for operational signals.
1. Sudden backlinks from suspicious domains
Cloners often leave internal links, asset calls, or copied references in place. A spike in low-quality backlinks can be an early sign.
2. Customer complaints about orders you cannot find
If customers reference order confirmations, discounts, or websites your team does not recognize, investigate immediately.
3. Unusual discount language using your brand
Scam clones often rely on aggressive urgency like “80% off today only,” “warehouse clearance,” or “closing sale” language that does not match your actual pricing strategy.
4. Ads promoting your brand from unauthorized accounts
Clone websites are frequently paired with ads on Google, Facebook, Instagram, and TikTok to scale traffic fast.
5. New domains containing your brand name or product terms
Lookalike registrations, country-code variations, and typo domains are common precursors to cloning attacks.
6. Product pages or images appearing outside your approved channels
If your catalog appears on standalone webshops you do not operate, investigate whether the site is reselling, cloning, or both.
7. Checkout pages that imitate your flow but use different payment endpoints
This is a high-risk signal because the site may be collecting payment details directly.
8. Support volume rises while site analytics do not
When customer confusion increases but your official sessions do not, diverted traffic may be landing elsewhere.
9. Search results surface unfamiliar domains for branded queries
Clone sites often try to capture traffic from search before the brand notices.
How to prevent website cloning
Prevention will not eliminate the threat completely. But it can make cloning harder, reduce the value of copied assets, and improve your ability to respond fast.
Build a strong legal baseline
Every brand should maintain clean, current IP ownership before a cloning incident occurs, not scramble to establish it after one is discovered. Legal coverage is what determines how quickly enforcement can be escalated and whether formal action is available when the situation requires it.
That means:
- Registered trademarks where possible
- Clear copyright notices
- Terms of use and content ownership language
- Archived versions of your site and assets
- A record of official domains, subdomains, and authorized stores
This does not stop cloning on its own. But it strengthens your enforcement position when a copied site appears.
Harden the site technically
Technical hardening reduces the ease of copying but does not eliminate the risk. Determined attackers can rebuild the experience from front-end assets and screenshots even when the backend is locked down, so technical measures work best as one layer in a broader detection and response system, not as a standalone solution.
That includes:
- Patching CMS, theme, and plugin vulnerabilities
- Limiting unnecessary public asset exposure
- Reviewing bot defenses and rate-limiting policies
- Monitoring for suspicious scraping patterns
- Protecting APIs and feeds that expose product data
Protect your visual assets
Official product imagery is typically the fastest trust signal on a clone site — it’s what makes the fake storefront look credible to customers who already recognize your brand. Controlling how and where your images appear online is one of the most direct ways to reduce clone site effectiveness.
Use:
- Watermarks where commercially viable
- Controlled image distribution
- Reverse image monitoring
- A documented library of official brand assets for enforcement
Monitor domains continuously
New lookalike domains are often registered days or weeks before an active cloning campaign begins. Catching them early — before they have been used to redirect traffic or run ads — is what gives brands the window to act before customers are exposed.
The standard is to monitor for domain abuse regularly.
The friction is that manual monitoring does not scale across typo domains, country-code variants, and newly registered lookalikes.
Watch the channels that feed clone traffic
A clone site becomes dangerous when customers can find it, and most operators rely on paid ads, social content, or search placements to generate that reach quickly. Monitoring the channels that amplify clone traffic — not just the domain itself — is what determines how much harm a clone can do before it is removed.
That means monitoring beyond the domain itself:
- Google Search
- Google Ads
- Meta ads
- TikTok
- Marketplaces and reseller channels that link out to external stores
Keep a live inventory of official channels
Without a clear internal record of which domains, accounts, and sellers are official, teams often lose time during incident response trying to verify what is legitimate before they can act on what is not. A live inventory of official channels shortens that gap and helps avoid false positives when coordinating enforcement across multiple stakeholders.
Maintain a clear internal source of truth for:
- Official domains and subdomains
- Approved country sites
- Authorized resellers and distributors
- Active paid social accounts
- Official ad accounts and campaign identifiers
This reduces internal confusion during incident response and helps avoid false positives.
Manual monitoring vs scalable monitoring
| Approach | What it helps with | Where it breaks |
| Manual checks | Spot checks, customer support triage, one-off investigations | Too slow across new domains, ads, and repeated attacks |
| Security tooling only | Infrastructure visibility, traffic anomalies, scraping detection | Often misses impersonation context and off-domain abuse |
| Brand protection platform | Detection across domains, websites, ads, social media, marketplaces, and enforcement workflows | Requires onboarding, asset setup, and ongoing optimization |
The standard is to check for abuse regularly.
The friction is that regular manual searching cannot keep pace with clone campaigns that move across domains, ads, search results, and social accounts.
The pivot is to use automation for scale while keeping human expertise in the loop for high-risk verification, enforcement decisions, and complex escalations. That matters because clone-site enforcement is not only a volume problem. It is also a judgment problem. Brands need speed, but they also need accuracy to avoid false positives and misfires.
What to do if you discover a cloned website
A cloning incident should be handled like a brand-risk event, not just a content-theft complaint.
1. Confirm whether the clone is static or dynamic
Make a small, low-risk change on your official site, such as a minor footer update, then compare the clone. If the clone updates too, the operator may be scraping your site repeatedly.
2. Preserve evidence immediately
Evidence can disappear quickly once a scam operator notices scrutiny or takes the site offline. That is why brands should document the clone thoroughly before moving into enforcement.
- Capture full-page screenshots of the homepage and any key landing pages so you have a clear visual record of how the site presented itself to customers.
- Save copies of the product pages to show which items, prices, descriptions, and images were being used to impersonate your catalog.
- Document the checkout flow to determine whether the site is collecting payment details, redirecting to a third-party processor, or imitating your own purchase journey.
- Archive the contact page and FAQ page because these sections often reveal false business details, fake policies, or copied customer-service language.
- Pull source code snippets where relevant if your team needs to verify copied assets, reused tracking scripts, or technical signs of dynamic scraping.
- Record clear timestamps for each capture so you can prove when the infringing content was live and support later legal or enforcement actions.
- Save the ad creative and landing pages driving traffic to the clone because the website is often only one part of the scam. In many cases, the ads, social posts, or search placements are what make the clone dangerous at scale.
3. Assess business impact
Once the clone is confirmed, the next step is to measure how much risk it creates for the business. This helps teams decide how urgently to escalate and which stakeholders need to be involved.
- Identify the affected geographies so you know where customers are being targeted and whether the issue is limited to one market or spreading across regions.
- Confirm whether paid ads are involved because ad-driven clone campaigns can scale much faster than a standalone fake domain with no traffic source.
- Assess whether customer data may have been exposed so your team can determine if the incident is only a brand abuse issue or also a fraud and security issue.
- Check whether distributors or partners are being harmed since clone sites can undercut authorized sellers, create channel conflict, and trigger confusion across the distribution network.
- Determine whether the clone is linked to counterfeit fulfillment because some sites do more than steal payments. They may also ship fake goods that create additional reputational, legal, and customer-safety risks.
4. Block abusive access where feasible
If the clone is scraping dynamically, your technical team may be able to block the relevant IPs, bots, or abusive request patterns. This does not solve the entire problem, but it can reduce ongoing content harvesting.
5. Notify internal stakeholders fast
Website cloning is rarely just a legal issue or just a security issue. The faster the right teams are aligned, the faster the brand can contain exposure and respond consistently.
- Notify the ecommerce team first so they can validate which storefront assets, campaigns, and promotions have been copied and assess any impact on conversion or traffic.
- Bring in legal or IP counsel early to review trademark, copyright, and impersonation angles and guide the enforcement path.
- Alert security or IT if there are signs of data theft, credential capture, dynamic scraping, or broader technical abuse connected to the clone.
- Inform customer support so agents know how to identify affected customers, respond consistently, and flag new reports tied to the fake site.
- Loop in paid media if the clone is being promoted through Google Ads, Meta ads, or other paid channels, since ad removal may be as important as domain enforcement.
- Contact channel partners if affected when distributors, resellers, or regional teams may be receiving complaints, losing sales, or encountering customer confusion linked to the clone.
6. Launch multi-channel enforcement
If the clone is being amplified through search, ads, social media, and hosting infrastructure, those actions must be addressed in parallel, not one by one.
For the full process of filing with hosting providers, domain registrars, and search engines — including how to escalate when initial reports are ignored — see our guide to how to legally take down a website.
7. Decide how to communicate with customers
For active incidents, some brands need a temporary warning banner, help-center notice, or support macro that clarifies official domains and known scam patterns.
Website cloning incident response checklist
| Priority | Action | Why it matters |
| Immediate | Preserve screenshots, URLs, and evidence | Prevents loss of proof if the site changes or disappears |
| Immediate | Determine whether the clone is static or dynamic | Helps decide whether blocking scraper access may help |
| Immediate | Review ads, search results, and social posts linked to the site | Clones often depend on traffic amplification |
| Same day | Alert legal, ecommerce, security, and support teams | Reduces internal delays |
| Same day | Map all related domains and accounts | Attackers rarely operate from one asset only |
| Same day | Start enforcement and deindexing actions | Limits customer exposure |
| Ongoing | Monitor for relaunch attempts | Repeat incidents are common |
Case study – KEEN faced 1,400 complaints in a single day
Problem: When KEEN became the target of a spoofed-website campaign, the threat escalated fast. The brand went from zero to 1,400 customer complaints in one day after a scam ad on Facebook surfaced. The issue was not just one fake page. It was a fast-moving impersonation event that put customers, suppliers, and brand reputation at risk.
Solution: KEEN needed a scalable way to detect rogue websites continuously, not just respond after complaints arrived. Red Points provided 24/7 monitoring to identify and remove spoofed websites and adapt as attackers changed tactics.
Result: Red Points helped KEEN tackle thousands of online infringements, covering 666 domains with an 82.9% enforcement success rate and removing an estimated $5.7 million in counterfeit product value.
The lesson is clear: website cloning becomes expensive when detection starts after customer harm. Brands need visibility before the next complaint spike.
Why manual prevention and response usually fail
Most brands already know the baseline steps. They know they should monitor domains, review ads, preserve evidence, and report clone sites.
The problem is execution.
A small team cannot manually search Google, Bing, Google Ads, Meta, TikTok, domain databases, reseller sites, and standalone webshops every day and still respond fast enough. That is why website cloning becomes a whack-a-mole problem.
The standard is to monitor continuously.
The friction is that manual searching does not scale, and one-off reporting does not stop repeat operators.
The pivot is to use a system that detects, validates, prioritizes, and enforces across channels while still keeping expert review for ambiguous or high-risk cases. Red Points combines AI-driven detection with human-led validation and enforcement support so brands can move faster without losing control.
How Red Points helps brands respond to website cloning
Red Points tracks 1.4B+ domains, adds 250k new domains per day, and covers 99.5% of gTLDs and ccTLDs, giving brands a broader detection layer than occasional manual lookups.Red Points is not just a takedown vendor for single incidents. It is designed for the broader clone-site problem.
That includes:
- Detection across standalone websites, domains, search engines, paid ads, marketplaces, and social media
- Discovery through search engines, backlinks, domain databases, reverse image methods, and brand signals
- Multi-agent enforcement to improve speed and success on websites
- Centralized visibility through a standalone dashboard
- Monitoring that helps brands spot relaunches and repeated abuse
- A human-in-the-loop model so complex cases get expert review rather than blind automation
For brand teams, the value is not only more removals. It is better control over customer exposure, analyst time, enforcement speed, and repeat-attack prevention.
Final takeaway
Website cloning is not just a copy-paste nuisance. It is a scalable fraud model built to hijack the trust your brand has already earned.
If your team treats cloned websites as isolated takedown requests, you will keep reacting late. The more effective approach is to treat website cloning as a detection, prevention, and incident-response problem that spans domains, ads, search, social media, and enforcement.
That is the difference between removing one clone and reducing the chance that the next one reaches your customers first.
Frequently asked questions (FAQs)
In most cases, yes. Cloning a website usually involves unauthorized copying of copyrighted content, misuse of trademarks, deceptive impersonation, or fraud. The exact legal route depends on what was copied and how the clone is being used.
Not always. A cloned website may be used for phishing, but it can also be used to sell counterfeits, take payments without shipping goods, or divert customers from official channels. Phishing is one possible outcome, not the full definition.
They may scrape content, steal images, copy the front-end design, rebuild the template manually, or combine several methods. Some also use paid ads and social accounts to drive traffic to the clone.
Often, it is not a technical alert. It is a business signal, such as unfamiliar backlinks, fake ads using your brand, customer complaints about missing orders, or strange domains appearing for branded search queries.
No brand can eliminate the risk completely. The goal is to reduce exposure, make cloning harder, detect it earlier, and respond faster.
Usually all three. Website cloning is a cross-functional problem because it affects infrastructure, IP rights, customer trust, and revenue.
Because not every suspicious site is the same. Some cases require judgment about reseller status, fair use, brand context, and enforcement priority. Automation handles scale. Human expertise is vital for high-risk verification, reducing false positives, and making the right escalation calls.
It varies significantly depending on who hosts the site, which enforcement channels are used, and how complete your evidence is. Hosting provider complaints can result in action within 24 to 72 hours for providers with clear abuse policies and complete evidence. Domain registrar complaints typically take longer — several days to a couple of weeks. Search engine deindexing requests follow their own timelines, often 48 to 96 hours for Google once the request is submitted. Ad removal on Google and Meta can happen within hours if the ad is clearly policy-violating. The most effective approach runs all channels in parallel rather than sequentially — a clone with its ads removed and its domain deindexed does far less damage even while the hosting-level takedown is still processing.