A customer clicks a Facebook ad offering a 70% discount on your best-selling product, lands on a professional-looking website, enters their payment details, and either receives a counterfeit item or nothing at all. A few hours later, your support team gets the complaint. By then, the scam may already be running across multiple domains, ads, and social accounts.
That is what makes fraud websites so dangerous. They are not just fake pages sitting quietly on the internet. They are active scam vehicles built to steal payments, capture personal data, divert traffic, misuse your brand, and damage customer trust at scale.
TL;DR – Key takeaways
- A fraud website is any website built to deceive users for financial gain, data theft, impersonation, counterfeit sales, or traffic diversion.
- Fraud websites overlap with fake websites and cloned websites, but they are not identical. The defining feature is the scam outcome, not only the site’s appearance.
- The biggest risks are customer harm, payment fraud, data exposure, revenue diversion, chargebacks, brand damage, and support overload.
- Not all fraud websites operate the same way. Some steal payment details, some take money without shipping, some ship counterfeits, and some exist mainly to harvest credentials.
- The right first step is not always a takedown request. Brands need to classify the fraud pattern, assess business impact fast, and coordinate the right internal response.
- Manual response breaks down when fraud websites are amplified through ads, domains, search, social media, and marketplaces.
- Fraud campaigns do not stay contained within a single domain — the same operation typically spans ads, social media, search results, and multiple domains simultaneously, which is why enforcement must address all channels in parallel rather than sequentially.
How to report a fraud website: where to file and who to contact
If you have already found a fraud website and need to report it, these are the main channels available. Filing across multiple channels simultaneously is more effective than filing sequentially — each targets a different layer of the scam’s infrastructure.
Google Safe Browsing
Report the URL at safebrowsing.google.com/safebrowsing/report_phishing/. Once flagged, Google Safe Browsing adds the site to its blocklist — which triggers warning screens in Chrome, Firefox, and Safari before users reach the page. This is the fastest way to reduce customer exposure while the hosting-level takedown is still being processed. For a step-by-step walkthrough of how to report a scam site to Google, including deindexing and DMCA requests, see our dedicated guide.
The domain registrar (via ICANN lookup)
Go to lookup.icann.org, enter the fraud website’s domain, and find the registrar listed under “Registrar Information.” Most registrars publish an abuse contact email — typically abuse@[registrar].com — in the ICANN record. File an abuse complaint with a clear description of the fraud, the domain name, and any supporting evidence. Registrar complaints can result in domain suspension, which takes the site offline entirely rather than just removing content. For a full guide to reporting and taking down illegal sites impersonating your brand, including evidence gathering and cease and desist letters, see our step-by-step walkthrough.
The hosting provider (via WHOIS)
Use a WHOIS tool (whois.com or the ICANN lookup above) to identify the hosting provider. Most hosting providers list an abuse email or abuse form in their support documentation. A valid DMCA notice or abuse complaint to the host requests removal of the infringing content from the server. If the site is behind Cloudflare, file first with the actual hosting provider and simultaneously at abuse.cloudflare.com/dmca.
Google Search (for deindexing)
File a legal removal request through Google’s reporting tools at support.google.com/legal/troubleshooter/1114905. For DMCA-based copyright infringement, use the copyright removal form. For phishing or malware, report through Google’s Safe Browsing tool above. Deindexing cuts off organic search traffic to the fraud site while the hosting-level takedown is still processing.
Paid ad platforms (if ads are amplifying the fraud site)
If the fraud website is being promoted through Google Ads, report the ad at support.google.com/google-ads/troubleshooter/4578507. For Meta ads on Facebook or Instagram, use the three-dot menu on the ad and select “Report Ad.” Removing the ads is often more urgent than removing the site itself — ads can scale exposure in hours, whereas an unamplified fraud site may have limited reach.
FBI Internet Crime Complaint Center (IC3)
File at ic3.gov if the fraud has resulted in financial loss or involves wire fraud, identity theft, or other federal crimes. IC3 reports are reviewed by FBI analysts and shared with appropriate law enforcement agencies. For US-based incidents, this is the primary government fraud reporting channel.
FTC (US Federal Trade Commission)
File at reportfraud.ftc.gov. FTC reports contribute to a central database used by law enforcement agencies to identify fraud patterns and build cases against serial operators. The FTC does not investigate individual complaints, but volume from multiple reporters increases the likelihood of enforcement action against a particular fraud network.
Social platforms (if the fraud site is promoted via social media)
Report fake profiles, pages, or posts promoting the fraud site directly on the platform where they appear. Facebook, Instagram, TikTok, and X each have in-app reporting flows for fraud and impersonation. Removing the social amplification — fake pages, accounts, and posts — is as important as reporting the website domain itself.
What is a fraud website?
A fraud website is an illegitimate website designed to deceive users into handing over money, payment details, credentials, or personal information. Some fraud websites impersonate a single brand. Others imitate multiple brands, categories, or shopping formats to widen the scam.
For businesses, the problem is not only that the site exists. The problem is what the site is trying to do.
A fraud website may be used to:
- Steal payment card details
- Take orders and never ship products
- Sell counterfeit goods
- Harvest customer credentials or personal data
- Divert traffic away from official websites and authorized distributors
- Exploit temporary promotions, urgency, or seasonal campaigns
This is why fraud websites should be treated as a business risk issue, not just a domain or content issue.
Fraud website vs fake website vs cloned website
A fraud website is the broadest risk category in this article. It describes a site built to deceive users and generate financial or data-driven harm. The focus is on the scam objective.
A fake website is a site that impersonates a brand, misuses brand assets, or misleads customers into believing the site is legitimate. The focus is on brand impersonation and unauthorized use.
A cloned website is a specific type of fake or fraud website created by copying the design, structure, images, content, or checkout flow of a real website. The focus is on replication.
| Term | What defines it | Main business concern |
| Fraud website | A site built to deceive users for money, data, or other gain | Scam risk, customer harm, financial exposure |
| Fake website | A site impersonating a brand or posing as a legitimate business | Brand misuse, customer confusion, takedown need |
| Cloned website | A copied version of a real site designed to look authentic | Replication of assets, storefront abuse, repeat cloning |
A cloned site can also be a fake site. A fake site can also be a fraud site. But not every fraud website needs to be a close visual clone. Some are crude, fast-moving scam stores designed to look “good enough” for one short campaign.
That distinction matters because the response should match the threat. A cloned website may require asset-level investigation. A fake website may demand strong takedown execution. A fraud website often requires faster triage around customer harm, payment risk, ad amplification, and internal escalation.
If your situation is primarily about a site cloning your storefront design, images, and checkout flow, see our dedicated guide to website cloning. If the issue is a fake website impersonating your brand specifically, see our guide to how to take down a fake website.
The main types of fraud websites brands face
Fraud websites do not all work the same way. Identifying the pattern early helps determine how urgently to escalate and what action path to take first.
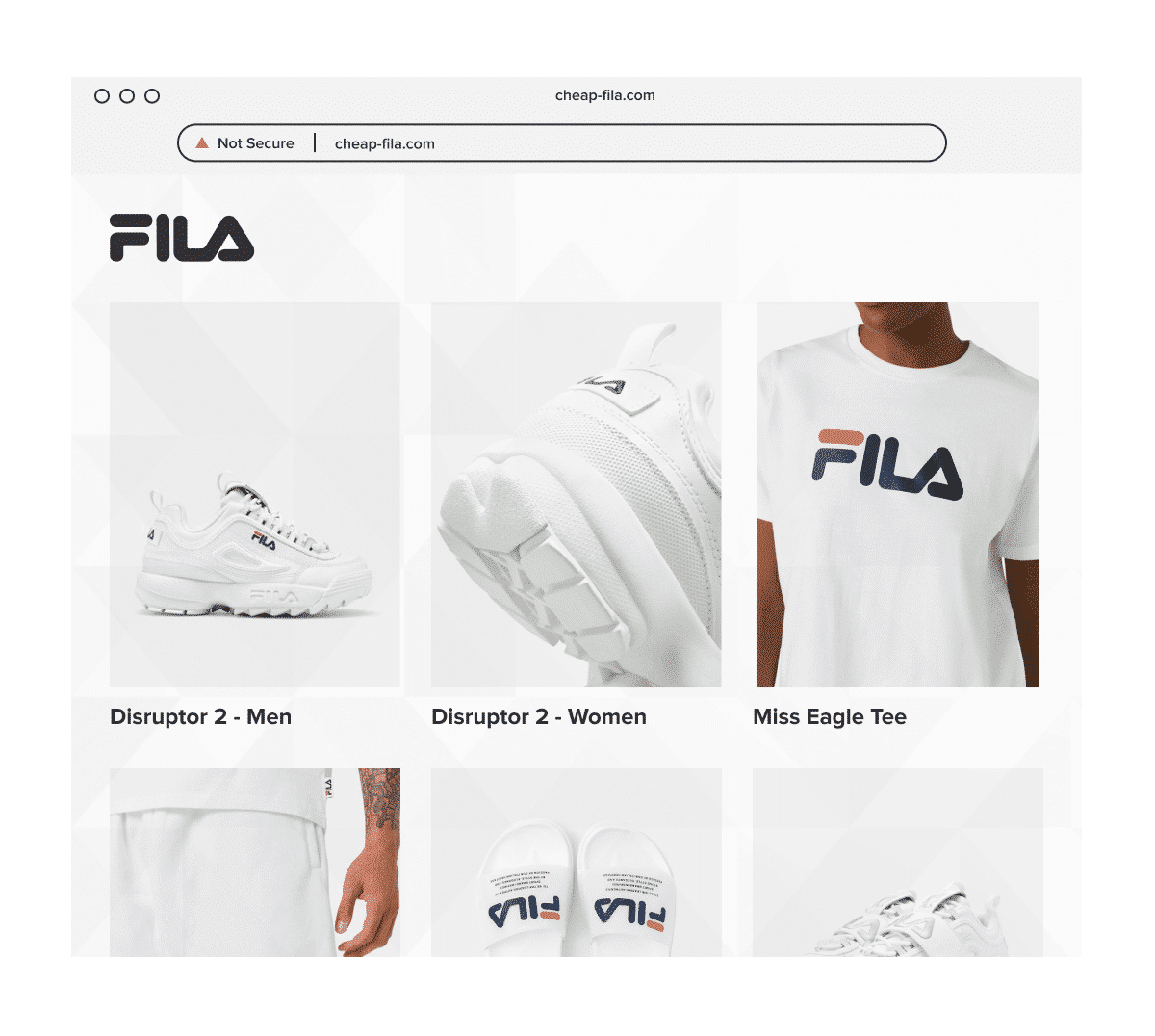
Fake checkout websites
These sites are designed to collect payment card details or personal information through a checkout flow that looks legitimate. In some cases, the scam ends at data capture. In others, victims are charged and never receive anything. This type of site is one of the most common forms of business identity theft affecting brands with established ecommerce presence.
Non-delivery scam stores
These websites accept payment but never fulfill the order. They often use aggressive discounts, limited-time offers, and copied product imagery to convert quickly before complaints appear.
Counterfeit storefronts
These sites sell products that imitate the original brand. The buyer receives something, but it is fake, poor quality, unsafe, or materially different from what they expected. See our guide on how to report websites selling counterfeit goods for step-by-step enforcement options.
Phishing or credential-harvest websites
These websites are built to collect logins, emails, addresses, or other personal information. They may mimic account pages, support portals, or branded customer-service flows. For a detailed breakdown of how to identify and report phishing sites through registrars, hosting providers, and Google, see our dedicated guide.
Flash-sale and liquidation scam sites
These scams lean on urgency. They often claim “warehouse clearance,” “brand closing sale,” or “today only” pricing to drive impulse purchases before users stop to verify legitimacy.
Ad-driven scam funnels
Some fraud websites only become visible because paid ads push traffic into them. In those cases, the website is only one part of the attack. The ad account, creative, and landing-page network are all part of the scam operation.
Multi-brand fraud websites
These websites use multiple brands illegitimately, often to cast a wider net and maximize conversion. They may rotate logos, categories, and copied content depending on the campaign.
How to tell which fraud pattern you’re dealing with
The faster you classify the fraud pattern, the faster you can decide whether the priority is customer communication, evidence collection, payment-risk containment, ad removal, or full enforcement.
Start by looking at the website’s behavior, not just its design.
If the site has a convincing checkout but no evidence of fulfillment, you may be looking at a payment theft or non-delivery scam.
If it uses your official product imagery and offers branded goods at unrealistic prices, it may be a counterfeit storefront.
If it imitates account access, password reset flows, or support pages, it may be a credential-harvest or phishing site.
If traffic appears to be coming from Google Ads, Meta ads, Facebook, Instagram, or TikTok, the fraud may be operating as an ad-driven campaign rather than a single rogue website.
If the same operator appears to be using multiple domains, changing creative frequently, or reusing copied assets, you may be looking at a repeat scam actor rather than an isolated site.
The goal at this stage is not legal perfection. It is fast classification so the right teams can move before more customers are exposed.
How to assess business impact fast
Once the fraud pattern is clear, the next priority is to determine how much exposure the business has and where the damage is likely to show up first.
Check affected geographies
Identify where users are being targeted. A fraud website hitting one country site is a different problem from a campaign spreading across multiple markets or language versions.
Determine whether paid ads are involved
Paid traffic increases urgency. A scam site with no amplification may stay limited. A scam site backed by Meta ads or search ads can scale exposure in hours.
Assess whether customer data may have been exposed
If the site includes a checkout, login page, or lead form, the incident may involve more than brand misuse. It may also trigger security, fraud, or privacy concerns.
Look for signs of counterfeit fulfillment
Some fraud websites steal money without shipping anything. Others ship fake goods. That difference matters because counterfeit fulfillment creates additional legal, reputational, and customer-safety risks.
Estimate the impact on support and reputation
Look for complaint spikes, unusual refund requests, chargeback patterns, or negative reviews that suggest customers are already associating the scam with your brand.
Check for channel or distributor harm
Fraud websites can distort pricing, confuse authorized sellers, and damage trust across the distribution network, especially if the scam appears to be an official sales channel.
Who needs to be involved internally
Fraud websites are rarely owned by one team alone. The right response depends on getting the correct stakeholders aligned quickly.
Ecommerce
The ecommerce team should validate whether storefront assets, promotions, pricing language, or checkout elements have been copied and assess any traffic diversion or conversion impact.
Legal or IP counsel
Legal teams help determine the enforcement route, evaluate trademark and copyright misuse, and support evidence preservation for escalations.
Security or IT
Security should be involved when customer data, credentials, payment details, or technical abuse may be part of the incident.
Customer support
Support teams are often the first to hear about fraud websites through confused customers, refund questions, or complaints about missing orders.
Paid media
If ads are amplifying the scam, paid media teams need to help identify unauthorized creatives, landing pages, and account-level abuse.
Channel or distribution teams
If the fraud website is creating reseller confusion, undercutting pricing, or damaging partner trust, relevant channel teams need visibility immediately.
Fraud website response matrix
| Fraud pattern | Main risk | First teams to involve | First response priority |
| Fake checkout site | Payment theft and customer data exposure | Security, ecommerce, legal | Preserve evidence, assess payment exposure, contain risk |
| Non-delivery scam store | Revenue theft, complaints, chargebacks | Ecommerce, customer support, legal | Capture evidence, assess customer harm, start enforcement |
| Counterfeit storefront | Brand damage, safety risk, diverted sales | Brand protection, legal, channel teams | Validate product misuse, map related channels, enforce |
| Phishing or credential-harvest site | Credential theft, privacy exposure | Security, legal, support | Escalate urgently, preserve proof, notify affected teams |
| Ad-driven scam campaign | Rapid customer exposure at scale | Paid media, brand protection, legal | Remove ads and landing pages together |
| Multi-brand scam site | Broad reputational and enforcement complexity | Legal, brand protection, investigations | Map brand misuse, prioritize harm, coordinate action |
The point of this matrix is simple: not every fraud website should trigger the exact same playbook.
Why manual response fails when scams go multi-channel
Most brands know the basics. They know they should review suspicious sites, preserve evidence, and report abuse. The problem is that fraud campaigns do not stay neatly contained inside one domain.
A single fraud website may be connected to:
- Lookalike domains
- Google Search results
- Google Ads
- Meta ads
- Facebook pages
- Instagram profiles
- TikTok posts or accounts
- Marketplace listings linking out to external stores
That is where manual response starts to break down.
The standard is to investigate and report suspicious websites quickly.
The friction is that manual searching cannot keep up when the same scam moves across domains, ads, social media, and search placements. Teams get stuck in a whack-a-mole cycle, handling one URL at a time while the campaign continues somewhere else.
The better model is to combine continuous detection, cross-channel visibility, and human review for the cases that require judgment. Automation helps with scale. Human expertise is still essential for high-risk verification, prioritization, and complex enforcement decisions. For a comprehensive overview of how modern brands structure their defenses across all these channels, see our complete guide to brand protection.
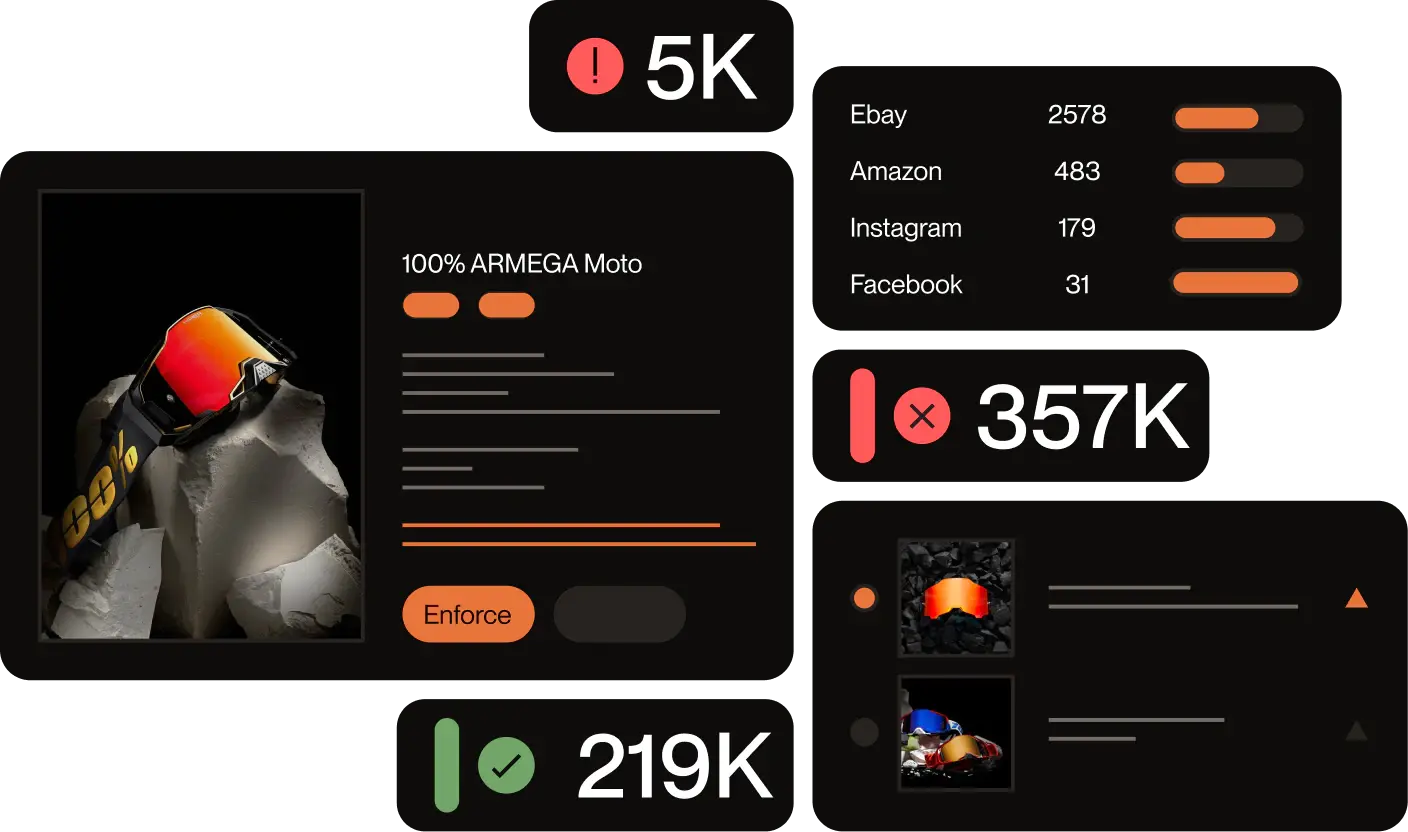
Case study – Burton stopped 4,000+ scam websites before they could steal customer payment details
Problem: Burton began seeing customers report purchases from websites they believed were official, only to discover that their payment details had been stolen or that orders never arrived. The team was trying to search, report, and escalate scam sites manually, but new fraudulent domains kept appearing just as quickly. Burton needed an always-on process that could catch threats before customers were exposed.
Solution: Burton shifted from reactive manual work to proactive detection with Red Points. The program used automated URL-based triggers to flag obvious impersonation sites, AI-driven detection to surface suspicious websites copying Burton’s layout, images, or pricing, and prioritization tools like allow lists, deny lists, and infringement prediction scoring to focus on the highest-risk cases first. Burton also worked closely with Red Points to refine rules and validations over time.
Result: Red Points helped Burton remove 4,600+ fraudulent websites, report 500+ sellers, and prevent 5,000+ fraudulent transactions. The case study also notes that Burton improved enforcement accuracy by 40% and moved from reacting after customer harm to stopping scam websites in real time.
The takeaway is clear: fraud website campaigns become far more expensive once the first complaint arrives. The brands that win are the ones that detect and contain them before customers ever reach the checkout.
How Red Points helps contain fraud website campaigns
The standard is to monitor suspicious sites, preserve evidence, and report them for removal.
The friction is that this process becomes slow and fragmented when fraud websites operate across domains, search engines, social media, paid ads, and linked scam assets.
This is where Red Points helps brands move from reactive reporting to coordinated containment.
Red Points monitors 1.4 billion domains, adding 250,000 new domains per day with 99.5% gTLD and ccTLD coverage — giving brands detection coverage that manual searching cannot approach. Across all enforcement categories, the platform delivers a 94–95% enforcement success rate for 1,300+ brands, with 4.6 million enforcements per year spanning websites, domains, marketplaces, ads, and social media simultaneously.
Red Points combines:
- Detection across standalone websites, domains, search engines, social media, ads, and marketplaces
- Website discovery through search engines, backlinks, and domain databases
- Monitoring that helps brands identify repeat abuse and relaunch attempts
- Multi-agent enforcement to improve takedown speed and success on websites
- A standalone dashboard for centralized website visibility and collaboration
- Human-in-the-loop review so high-risk or ambiguous cases get expert judgment, not blind automation
For brands, that means fewer manual bottlenecks, faster response to high-risk incidents, and better control over customer exposure when fraud campaigns spread across channels.
Final takeaway
Fraud websites should not be treated as generic website abuse. They are active scam assets built to convert trust into money, stolen data, and brand damage.
The brands that respond best are not the ones that only know how to file a report. They are the ones that can classify the fraud pattern quickly, assess business impact early, involve the right teams, and contain the campaign before it spreads across more channels.
That is the difference between reacting to one bad site and controlling a fraud operation before it scales.
A fraud website is defined by the scam outcome, such as payment theft, non-delivery, credential harvesting, or counterfeit selling. A fake website is defined more broadly by impersonation and unauthorized brand use. Many sites are both, but the two terms are not always interchangeable.
Not always, but often. A cloned website becomes a fraud website when the copied site is used to deceive users for money, data, or other harmful gain.
Check whether the site has a live checkout, login flow, lead form, paid traffic source, or signs of active fulfilment. Those signals usually indicate immediate customer exposure.
Usually both, along with ecommerce and support when relevant. Fraud websites are cross-functional because they can affect intellectual property, customer trust, payments, data, and operations at the same time.
Because many scam websites only achieve scale once traffic is pushed into them through Google Ads, Meta ads, or social platforms. Removing the website without addressing the traffic source often leaves the campaign partially active.
Because fraud websites vary in severity, intent, and context. Automation handles scale, but human expertise is still critical for high-risk verification, prioritization, and deciding the right enforcement path.
Use a WHOIS or ICANN lookup tool — lookup.icann.org is the most reliable starting point. Enter the fraud website’s domain and look under “Registrar Information” for the domain registrar and, in many cases, the hosting provider. If the hosting details are hidden behind a privacy service, the registrar contact is usually still visible and is itself a valid reporting target. Once you have the hosting provider identified, search their support documentation for an abuse contact or abuse email — most major hosts publish one. If the site uses Cloudflare as a CDN, file at abuse.cloudflare.com/dmca and also track down the origin hosting provider separately.
Treat it as a brand incident, not just a domain complaint. First, preserve evidence — screenshots, URLs, ad creatives, and timestamps — before taking any action that might alert the operator. Then run parallel actions: report the site to the hosting provider, file with Google Safe Browsing, report any ads promoting it to the relevant ad platform, and deindex the URL through Google’s legal removal tools. If your trademark is registered, a registrar abuse complaint based on trademark misuse is often faster than a standard DMCA notice. For brand impersonation specifically, filing through the platform’s trademark IP process — rather than a generic abuse complaint — typically results in faster action.